The following is written by Zac Williamson, with inspiration and advice from Arnaud Schenk.
My fellow companions, my decentralized brothers and sisters. I wish to tell you a story, about complicated people and their struggles to resolve the wreckage of their contradictions. It is a story of humanity.
We are at a unique point in history and stand at the threshold of two worlds. One world is a propagation of our present, a status quo antebellum with all of its associated joys and sorrows.
There is another door, one hidden from view except for those with the sight to see it. You and I are here because we see a unique vision of the future, one of high technology and high ideals, that advance human beings from their status as a commodity resource in a globalized world, to free actors imbued with autonomy and purpose, who bow to no one.
I want to articulate this vision and examine the forces that drive us. Despite our successes and dedication it is clear that our current achievements fall short of our aspirations. We must reconcile this.
Bitcoin is not yet a credible threat to traditional currencies. Paying for goods and services with cryptocurrency is a niche luxury for the technologically well-connected. Decentralized autonomous organizations (DAOs) are yet to govern anything that is not a cryptocurrency project. A notable exception was ConstitutionDAO, which immediately failed in its goals due to the intrinsic limitations of trustless blockchain networks.
There are missing pieces in the technological armaments we have fashioned. I want to show you the missing pieces. I want to go back to the roots: what are the systems and frameworks we want to disrupt? Which properties do blockchain networks need for us to forge a conspiracy against the present, and fight for our vision of the future?
Control Factions
Reaching back into prehistory, humanity has been waging a war against itself – a war that pits the freedom and autonomy of individuals against the safety and control of institutions.
We want to be free. We want to be safe. This is the eternal contradiction.
To acquire safety we bind ourselves to institutions. Within these institutions, control factions form. They metastasize and act to entrench their power and influence by monopolizing human agency. This triggers inevitable conflict and revolt, which acts to reset the equilibrium.
How best we can resolve the contradiction between freedom and safety is a function of social organization, the quality of which is gated behind technological innovation.
Blockchain is one such technology. To identify what we need, we must identify the weaknesses of the institutions we seek to undermine, and tailor our strengths against them.
The competency crisis
Control factions have a fatal weakness: they reject competence.
Competent people threaten individuals within entrenched power structures. A competent subordinate is a threat to your power and privileges. This is the so-called “dictator trap”, but the mechanics at play extend to all power structures, from the boards of mega-corporations to the local residents association. But it’s not a dictator trap, it is an institution trap.
Power craves legibility and predictability and will act on these desires by exerting control – limiting agency and freedom of action.
Re-distributing institutional control
We want to undermine institutional control, and redistribute control down to smaller units of organization.
Blockchain technology enables such radical new forms of social organization that fall outside the frameworks of traditional institutions.
We possess a keystone technology that enables mass peer-to-peer coordination, initially of cryptocurrency assets but this can be generalized to anything with perceived value that can be given a digital fingerprint.
Blockchain networks have radically different incentive mechanisms to traditional modes of social organization.
Because blockchains are coordination engines. They enable individuals to coordinate on how to deploy their collective resources. This type of mass-coordination of personal resources is unique and will subtly act to profoundly re-distribute the existing power structures of the present.
Why? Blockchains weaken the fundamental value propositions of vertically integrated companies that extract a profit from information asymmetries. Individuals whose skills serve large institutions can more easily decide for themselves how best to apply their skills, without the need for the institution’s support frameworks. As a coordination engine, blockchain networks can efficiently combine the skills and capital required to execute grand ideas, as well as provide a digital market for resulting products.
A global marketplace of programmable money is one with profound information transparency. The ability of independent groups to analyze the market enables great efficiency and reduces information asymmetries. Though, does not delete them entirely.
In short, blockchain networks are pro-competency. They allow individuals to decide for themselves how their skills can best be utilized and deployed, instead of having that decided for them by a control faction. Competent people add value to the network and in doing so, provide another composable brick that others can use in their constructions. The raw incentives create a positive-sum game.
Missing pieces
What are the missing pieces?
The great difficulty in realizing our vision is the limited ability of current blockchains to reach into the real world.
We are not our online avatars. We exist in a physical space and we have physical needs that must be satisfied. We are bound to networks of obligation and responsibility that societies depend upon to maintain social order. We cannot live in an NFT.
The real world matters. Without a way of linking real-world identities to blockchains, the grand cypherpunk vision for blockchain can never be fully realized – only a neutered form of primitive electronic sovereignty.
The new information networks: composable privacy
The new information networks we are building lack a key ingredient: composable privacy.
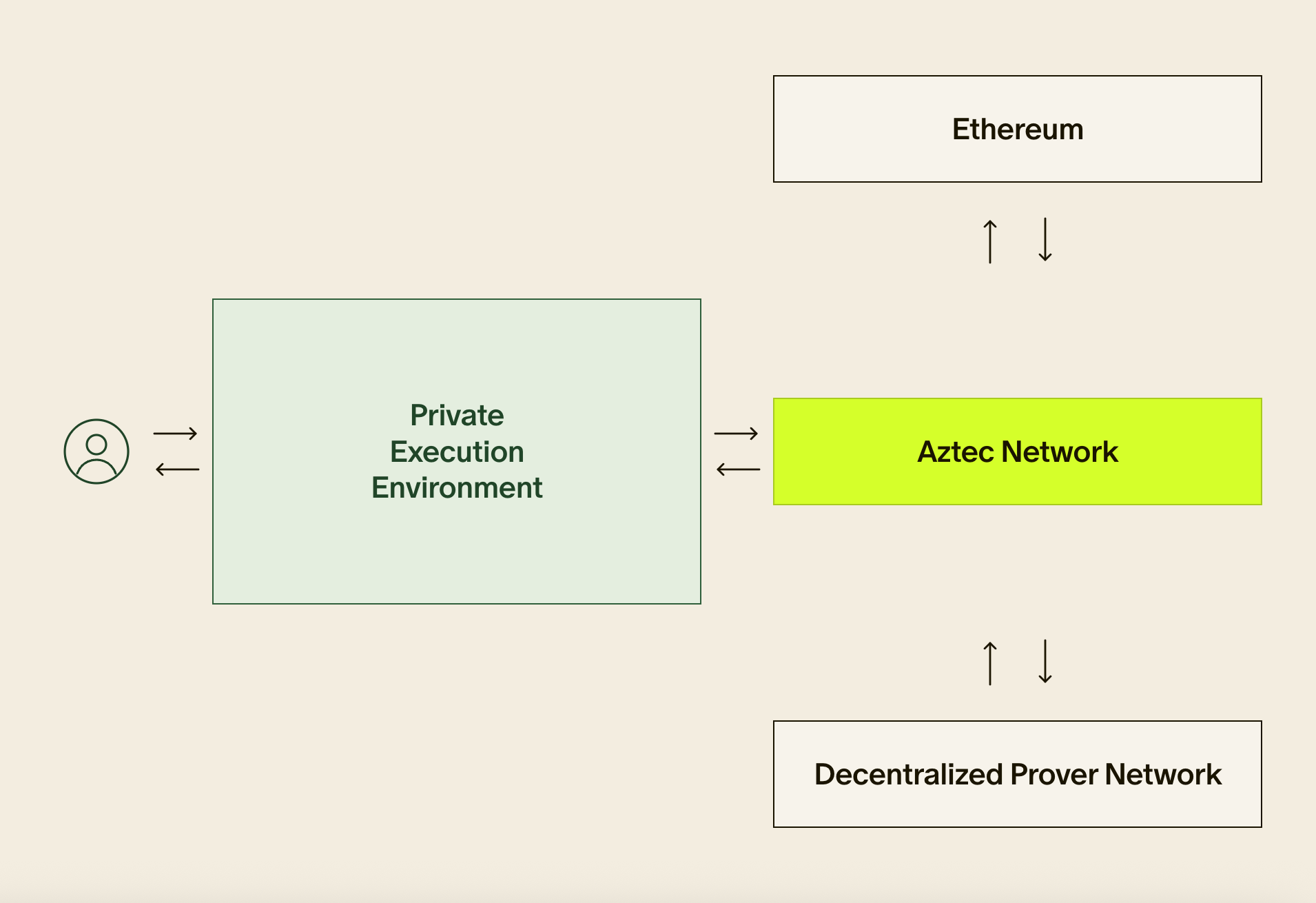
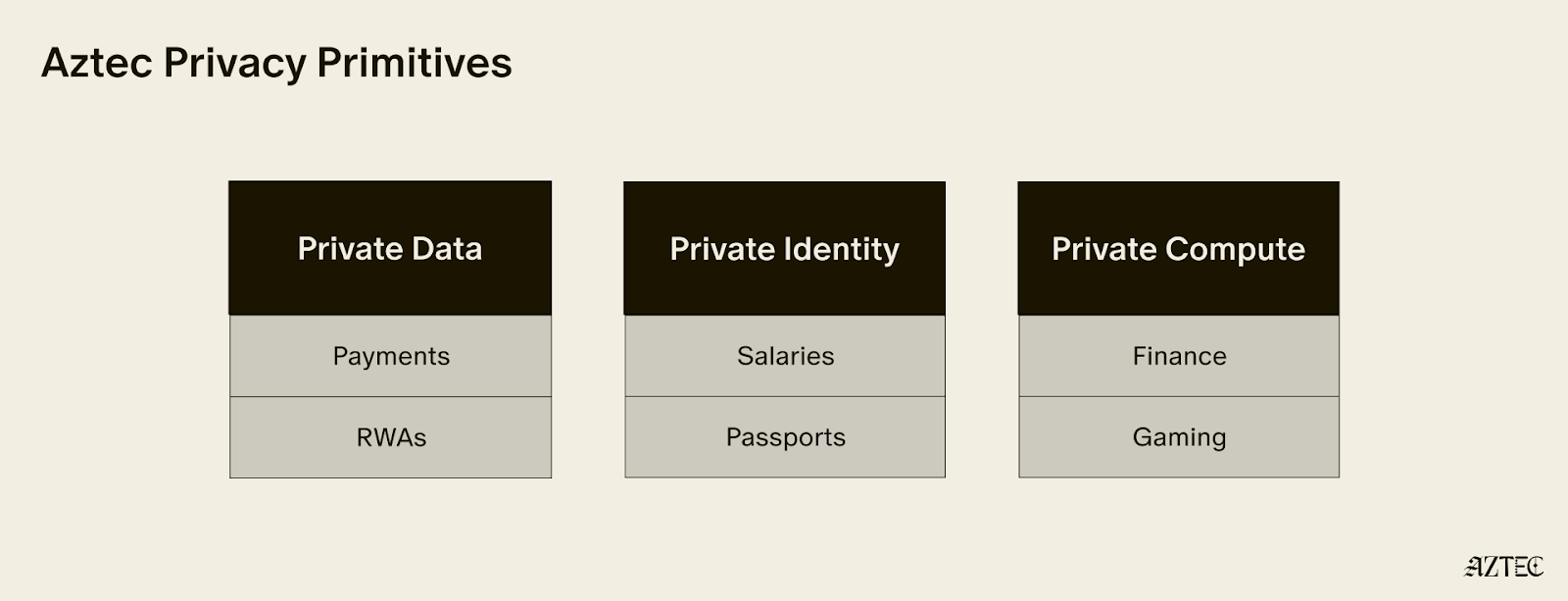
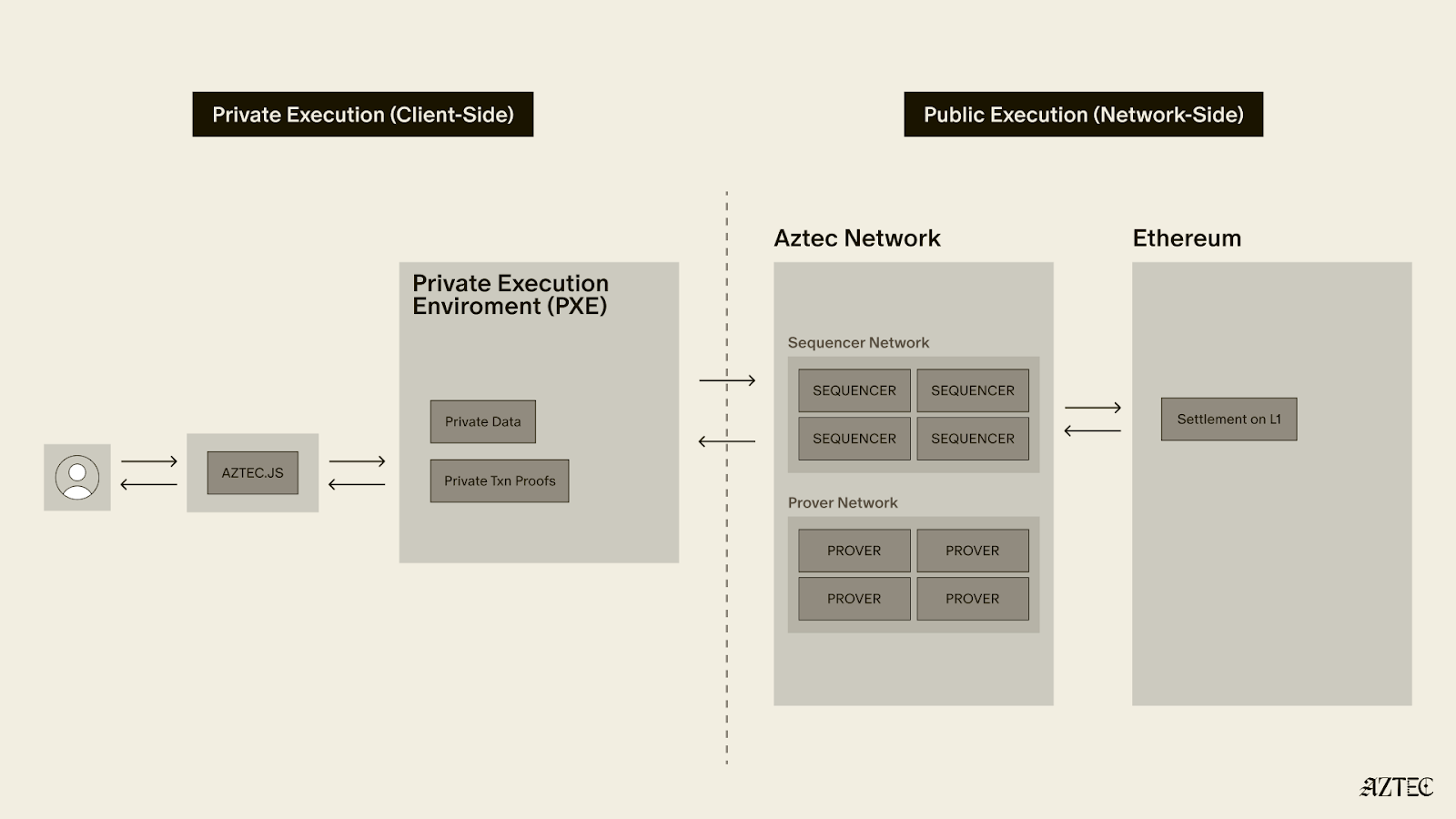
By using novel cryptography, we can turn blockchains into encrypted ledgers where transactions hide their execution from observers. Identities can be encrypted, but still used to prove statements about the user, and without involving an additional institutional third party. e.g. “I have a U.S. passport”, “I have a digital driving license”, “I have a Twitter account with over 1,000 followers”, “I signed in with a Google account”.
The effect of this is to build trust infrastructure that allows human beings to iteratively build trust between themselves and to do so rapidly and at scale.
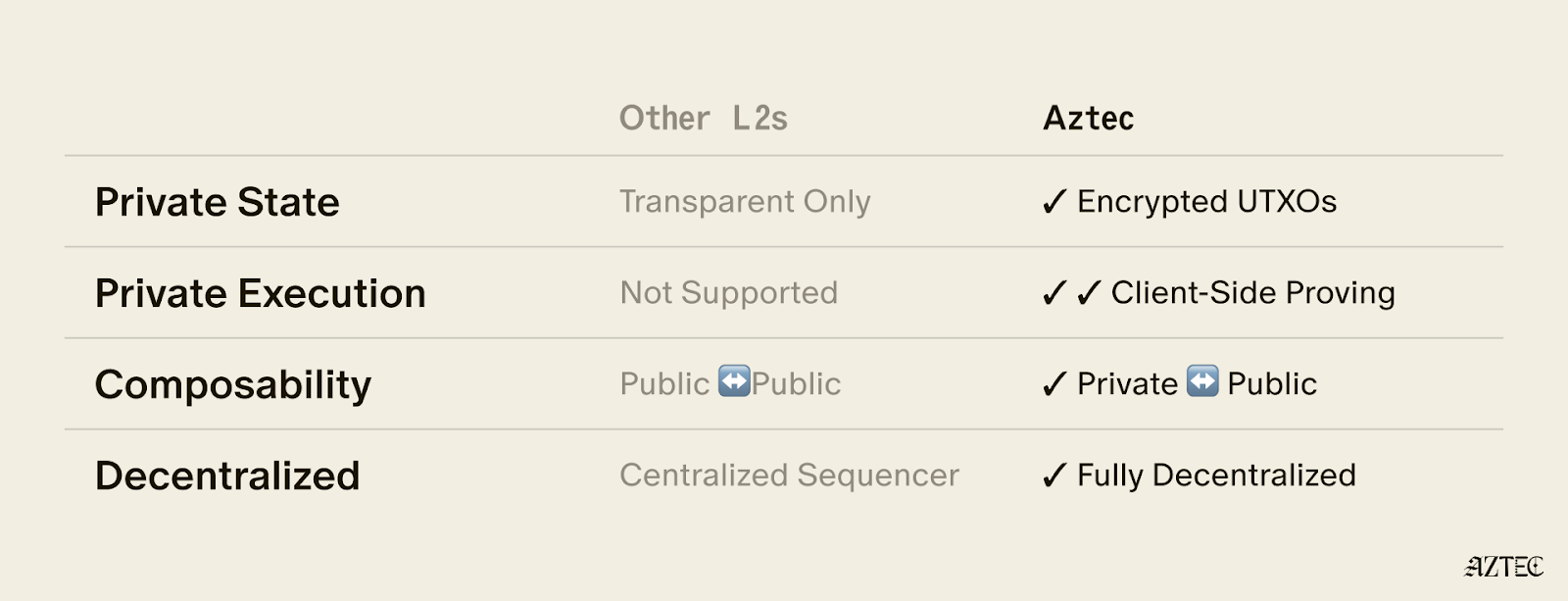
Programmable private blockchains stand to usher in a revolution in how distributed systems can be used. Without strong identity guarantees, the only workable governance mechanisms for distributed on-chain organizations are autocracy and plutocracy.
However, if past actions can be uniquely tied to a cryptocurrency account, it is possible to identify key stakeholders and to give them an accelerated role in governance. That enables a much more democratic architecture of governance systems.
Privacy technology is required to turn blockchains into the coordination engines they were always destined to be.
The future we are building does not outright destroy existing systems of control – it breaks them apart and replicates these systems on a smaller scale. Lower barriers to entry lead to greater competition and market fragmentation and act to limit the ability of distributed organizations to consolidate power.
Because coordination engines are pro-competency.
Privacy for the user, transparency for the protocol
There is a phrase I think we will hear much of over the coming years: privacy for the user, transparency for the protocol.
The capabilities of private programmable blockchains and the outcomes they enable are not commonly understood. A private blockchain is not one where all information and data are intrinsically hidden. They are hybrid systems where public and private data coexist. Application designers and users can choose which data is hidden.
Efficient markets require data transparency. Data relating to identity requires data confidentiality. The solution is applications where information that relates to assets is public, and information relating to users (e.g. who owns said assets) is private.
To create a privacy-preserving ecosystem it must be possible for confidential, transparent, and hybrid applications to directly interact with one another. Privacy is not an aftermarket add-on to be bolted onto a few select applications. Full composability is essential to develop a rich ecosystem.
Composability enables trust-building networks by allowing individuals to put core aspects of themselves on-chain, disclosing it only selectively and enabling distributed protocols to use these capabilities in a composable permissionless manner, without leaking information. Who are you? What have you done? What do you want to do? With privacy, we can disclose this information to smart contracts and hide it from people. These will form core primitives of our new information networks.
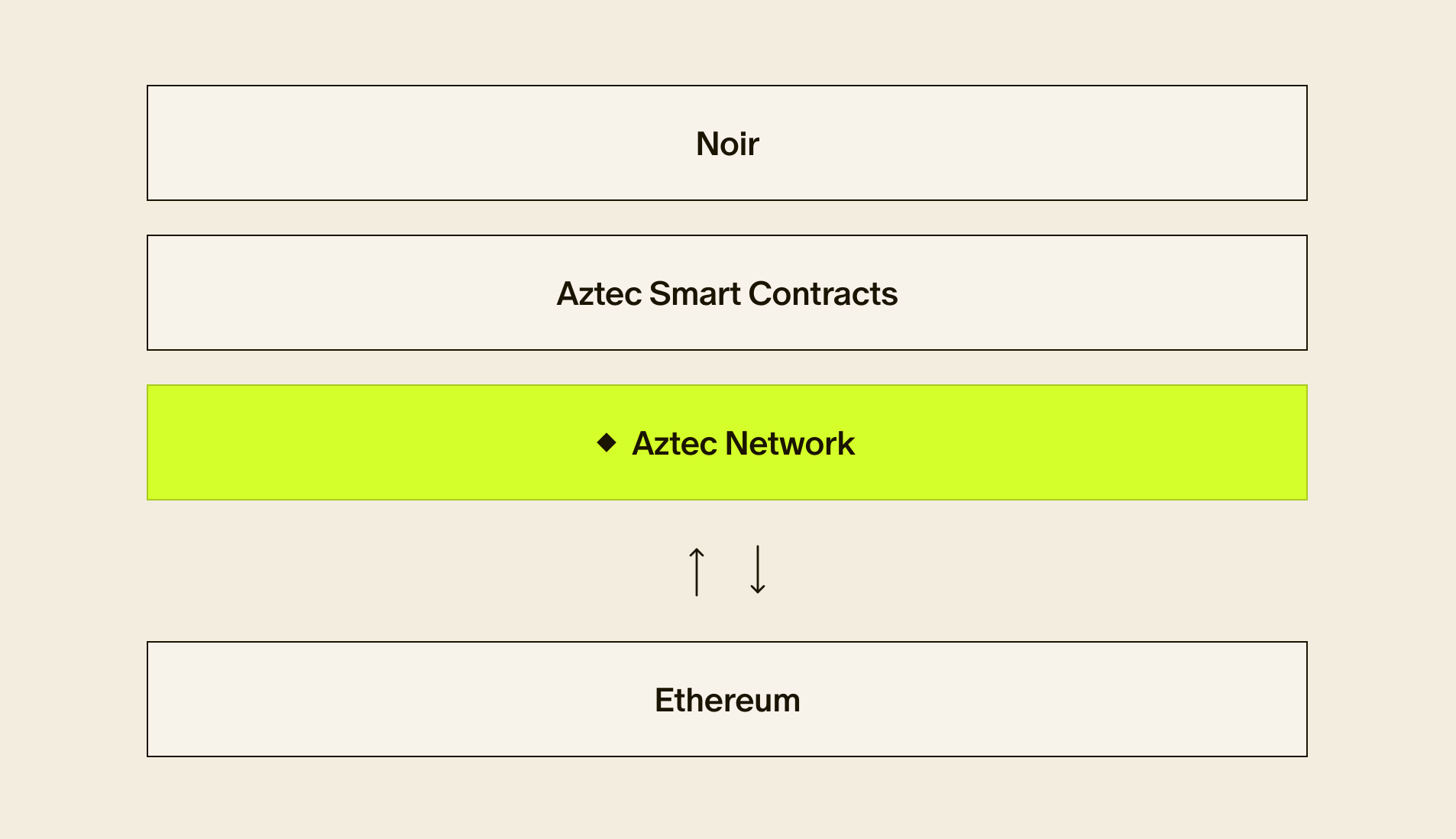
I have spent the last 6 years building exactly this, through building Aztec. Crafting the missing ingredient, privacy, via cutting-edge cryptography, zero-knowledge proofs, and raw engineering.
Values of the new information networks
Networks have values that are independent of their creators. Networks live or die on the quality of their network effects. This incentive gives network participants a shared motivation to expand the network. The more nodes that exist, the greater the value individual nodes can extract from the network. The manner in which the network changes itself to act on these motivations defines its intrinsic values.
What are the intrinsic values of permissionless programmable privacy networks like Aztec? We can derive these from the fundamental value proposition – to expose a rich ecosystem of composable, confidential applications, and to do this as a permissionless, decentralized network. This enables individuals and small groups to compete in industries dominated by large players leveraging large information asymmetries.
Such networks are, at their very core, pro-competency. If you have something useful to add to the network, you can. If you want to use existing network components in your product, go right ahead. No need to ask for permission from the network.
From this starting point we can anticipate the cycles of action and reaction that will drive networks like Aztec to adopt the following values over their lives:
- They are pro-emergence and pluralistic.
- They strongly desire individual autonomy and freedom of action.
- They are fiercely anti-elite, but not necessarily anti-elitism.
- Finally, they seek to undermine traditional frameworks of control and subjugation used to promote institutional stability.
Blockchain networks grow by harnessing the industry and enterprise of as many human souls as they can get their hands on.
Without mechanisms of coercion to fall back on, the network must ensure a positive-sum game for network participants who add value. These also happen to be values that I believe I strongly hold. This is not a coincidence. I started in web3 seven years ago building a marketplace for corporate debt on Ethereum and by degrees ended up building a distributed programmable privacy network on Ethereum. This was not due to some grand design but, I think, the cumulative effects of seven years of following my impulses. To find a place of belonging.
This feeling is something you may share – that the frameworks and systems produced by our societies offer none of us a true sense of belonging and purpose. But here, amongst our companions, we have found belonging through building a shared vision of a radical new world.
The road ahead
There is a long road to walk to realize the ambitions of the new information networks. The technology is barely capable and challenging to build. The architecture is novel and challenging to design. Convincing people to build on radical foundations to bootstrap a market is challenging. Building competitive infrastructure and tooling is challenging.
The challenge is irrelevant. We cannot become a generation scorned by our descendants for squandering the opportunity of a lifetime.
We will build and deploy the new information networks and by degrees will learn how to use them to chip away at the inequities of the status quo, and the social order that upholds it.
Equipped with such armaments and driven by our ideals, we will pull our ideas into reality. Together, we will forge our digital Eden.