
.jpg)
The First Feature Complete Privacy Stack is Here
Alpha is live: a fully feature-complete, privacy-first network. The infrastructure is in place, privacy is native to the protocol, and developers can now build truly private applications.
Nine years ago, we set out to redesign blockchain for privacy. The goal: create a system institutions can adopt while giving users true control of their digital lives. Privacy band-aids are coming to Ethereum (someday), but it’s clear we need privacy now, and there’s an arms race underway to build it. Privacy is complex, it’s not a feature you can bolt-on as an afterthought. It demands a ground-up approach, deep tech stack integration, and complete decentralization.
In November 2025, the Aztec Ignition Chain went live as the first decentralized L2 on Ethereum, it’s the coordination layer that the execution layer sits on top of. The network is not operated by the Aztec Labs or the Aztec Foundation, it’s run by the community, making it the true backbone of Aztec.
With the infrastructure in place and a unanimous community vote, the network enters Alpha.
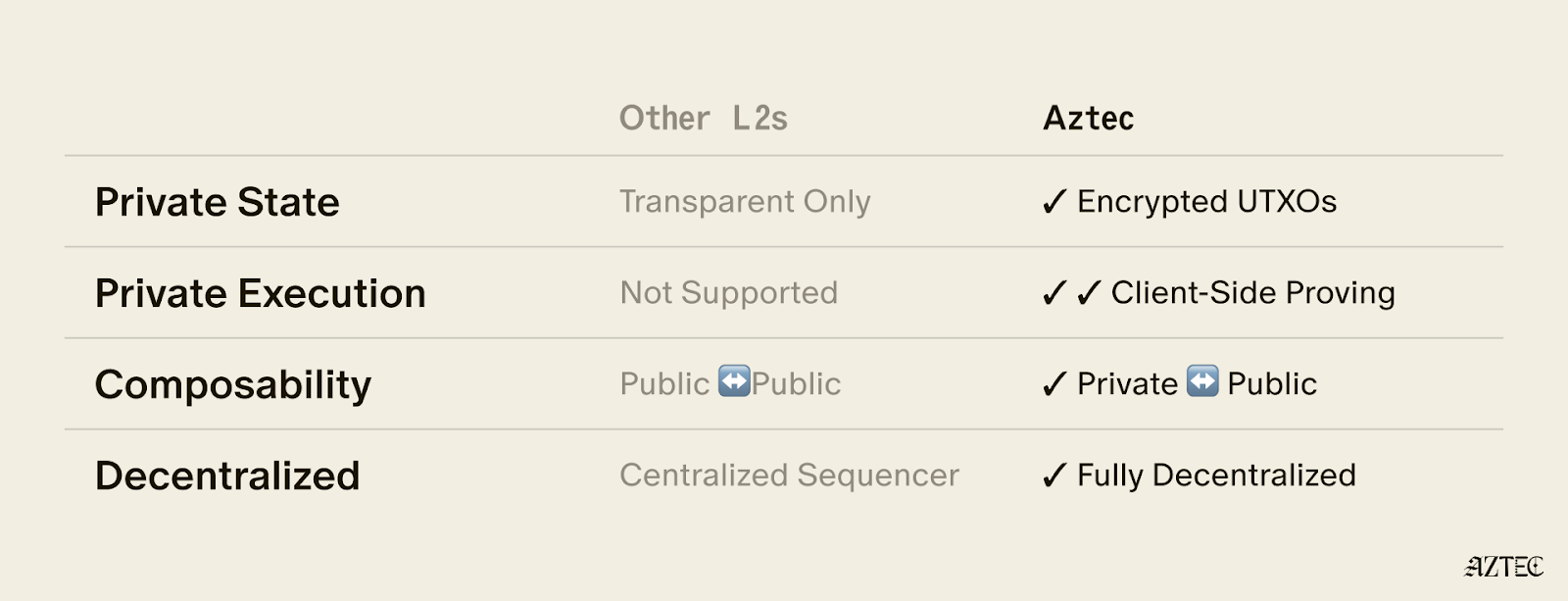
Alpha is the first Layer 2 with a full execution environment for private smart contracts. All accounts, transactions, and the execution itself can be completely private. Developers can now choose what they want public and what they want to keep private while building with the three privacy pillars we have in place across data, identity, and compute.
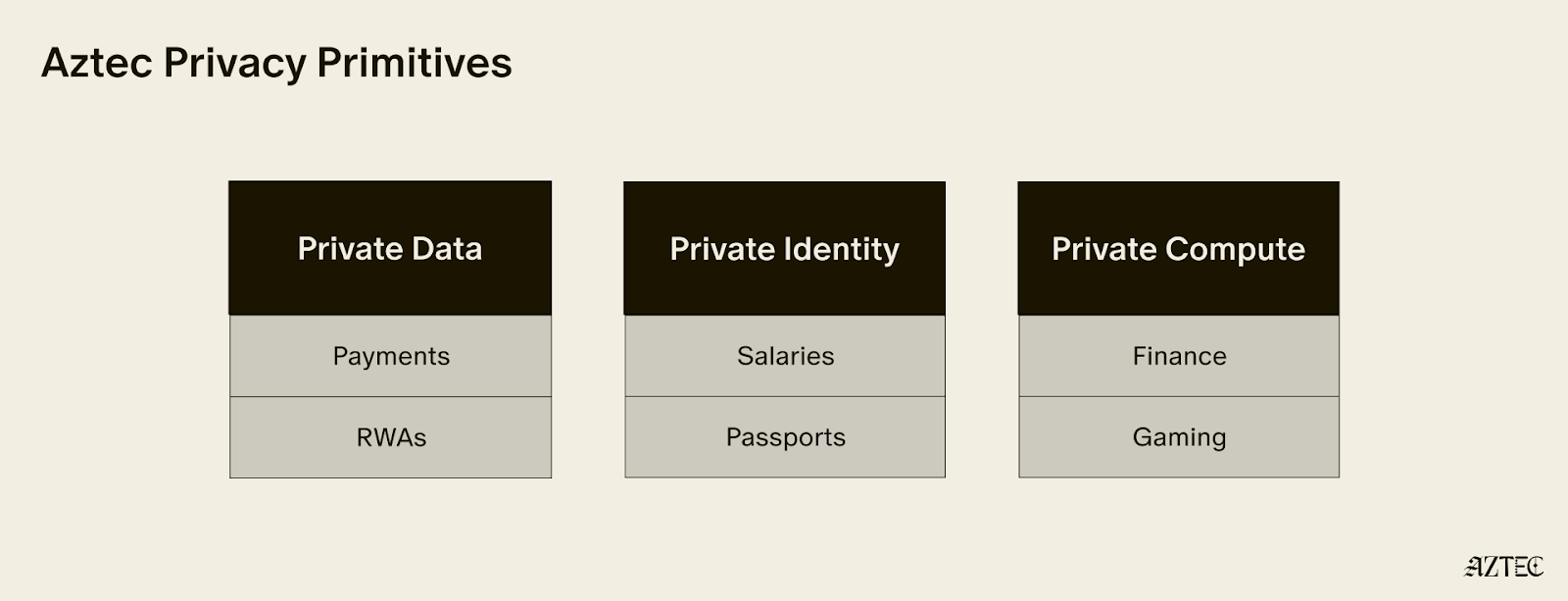
These privacy pillars, which can be used individually or combined, break down into three core layers:
Alpha is feature complete–meaning this is the only full-stack solution for adding privacy to your business or application. You build, and Aztec handles the cryptography under the hood.
It’s Composable. Private-preserving contracts are not isolated; they can talk to each other and seamlessly blend both private and public state across contracts. Privacy can be preserved across contract calls for full callstack privacy.
No backdoor access. Aztec is the only decentralized L2, and is launching as a fully decentralized rollup with a Layer 1 escape hatch.
It’s Compliant. Companies are missing out on the benefits of blockchains because transparent chains expose user data, while private networks protect it, but still offer fully customizable controls. Now they can build compliant apps that move value around the world instantly.
Developers can explore our privacy primitives across data, identity, and compute and start building with them using the documentation here. Note that this is an early version of the network with known vulnerabilities, see this post for details. While this is the first iteration of the network, there will be several upgrades that secure and harden the network on our path to Beta. If you’d like to learn more about how you can integrate privacy into your project, reach out here.
To hear directly from our Cofounders, join our live from Cannes Q&A on Tuesday, March 31st at 9:30 am ET. Follow us on X to get the latest updates from the Aztec Network.
On Wednesday 17 March 2026 our team discovered a new vulnerability in the Aztec Network. Following the analysis, the vulnerability has been confirmed as a critical vulnerability in accordance with our vulnerability matrix.
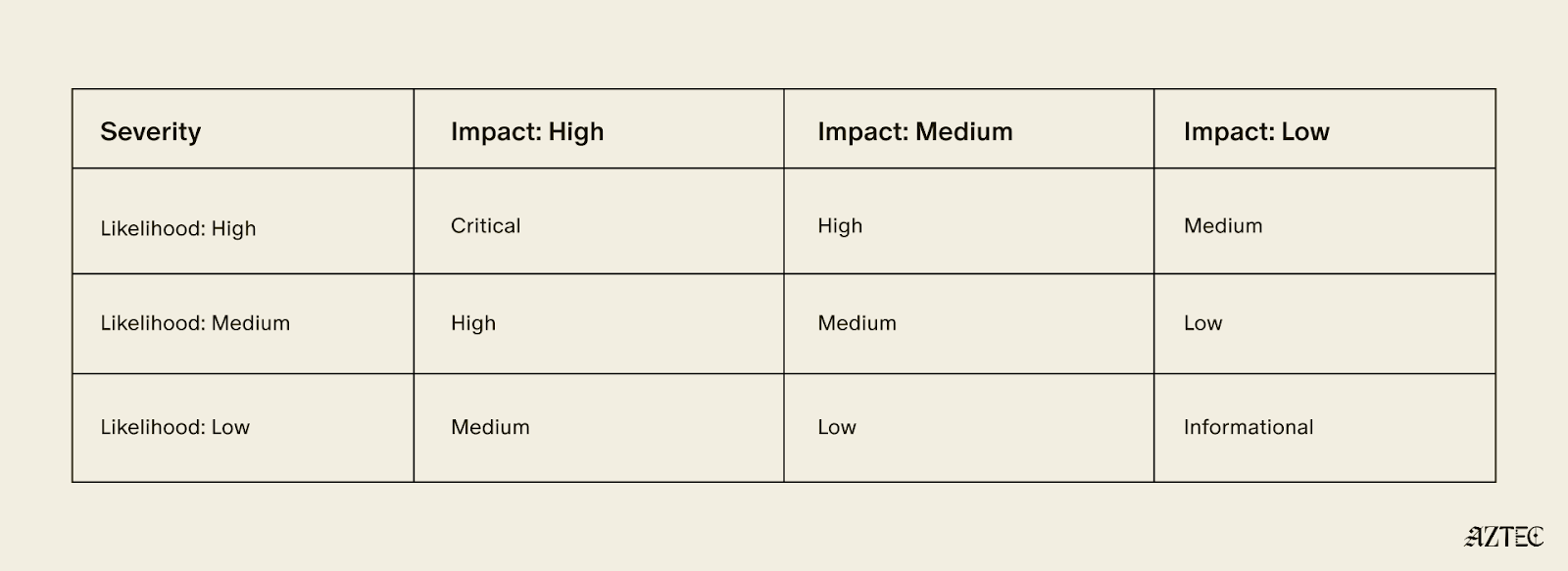
The vulnerability affects the proving system as a whole, and is not mitigated via public re-execution by the committee of validators. Exploitation can lead to severe disruption of the protocol and theft of user funds.
In accordance with our policy, fixes for the network will be packaged and distributed with the “v5” release of the network, currently planned for July 2026.
The actual bug and corresponding patch will not be publicly disclosed until “v5.”
Aztec applications and portals bridging assets from Layer 1s should warn users about the security guarantees of Alpha, in particular, reminding users not to put in funds they are not willing to lose. Portals or applications may add additional security measures or training wheels specific to their application or use case.
We will shortly establish a bug tracker to show the number and severity of bugs known to us in v4. The tracker will be updated as audits and security researchers discover issues. Each new alpha release will get its own tracker. This will allow developers and users to judge for themselves how they are willing to use the network, and we will use the tracker as a primary determinant for whether the network is ready for a "Beta" label.
We have identified a vulnerability in barretenberg allowing inclusion of incorrect proofs in the Aztec Network mempool, and ask all nodes to upgrade to versions v.4.1.2 or later.
We’d like to thank Consensys Diligence & TU Vienna for a recent discovery of a separate vulnerability in barretenberg categorized as medium for the network and critical for Noir:
We have published a fixed version of barretenberg.
We’d also like to thank Plainshift AI for discovery, reproduction, and reporting of one more vulnerability in the Aztec Network and their ongoing work to help secure the network.
Decentralization is not just a technical property of the Aztec Network, it is the governing principle.
No single team, company, or individual controls how the network evolves. Upgrades are proposed in public, debated in the open, and approved by the people running the network. Decentralized sequencing, proving, and governance are hard-coded into the base protocol so that no central actor can unilaterally change the rules, censor transactions, or appropriate user value.
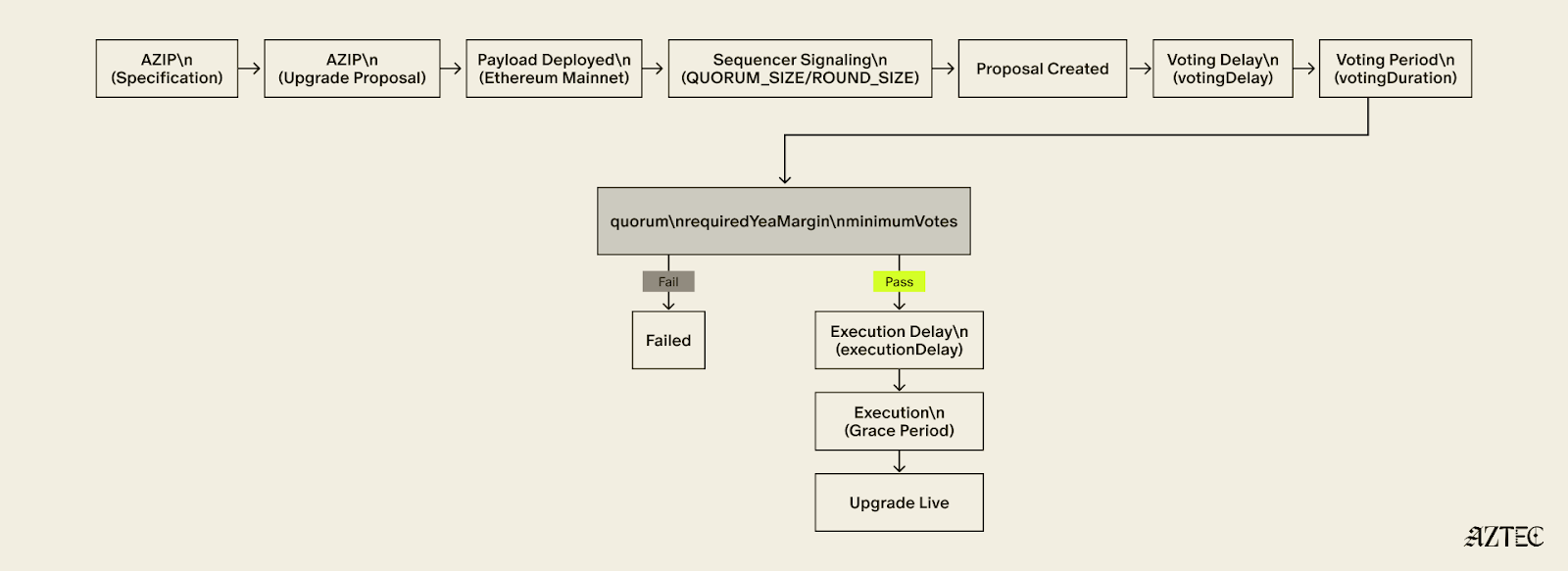
The governance framework that makes this possible has three moving parts: Aztec Improvement Proposal (AZIP), Aztec Upgrade Proposal (AZUP), and the onchain vote. Together, they form a pipeline that takes an idea to a live protocol change, with multiple independent checkpoints along the way.
Every upgrade starts with an AZIP. AZIPs are version-controlled design documents, publicly maintained on GitHub, modeled on the same EIP process that has governed Ethereum since its earliest days. Anyone is encouraged to suggest improvements to the Aztec Network protocol spec.
Before a formal proposal is opened, ideas live in GitHub Discussions, an open forum where the community can weigh in, challenge assumptions, and shape the direction of a proposal before it hardens into a spec. This is the virtual town square: the place where the network's future gets debated in public, not decided behind closed doors.
The AZIP framework is what decentralization looks like in practice. Multiple ideas can surface simultaneously, get stress-tested by the community, and the strongest ones naturally rise. Good arguments win, not titles or seniority. The process selects for quality discussion precisely because anyone can participate and everything is visible.
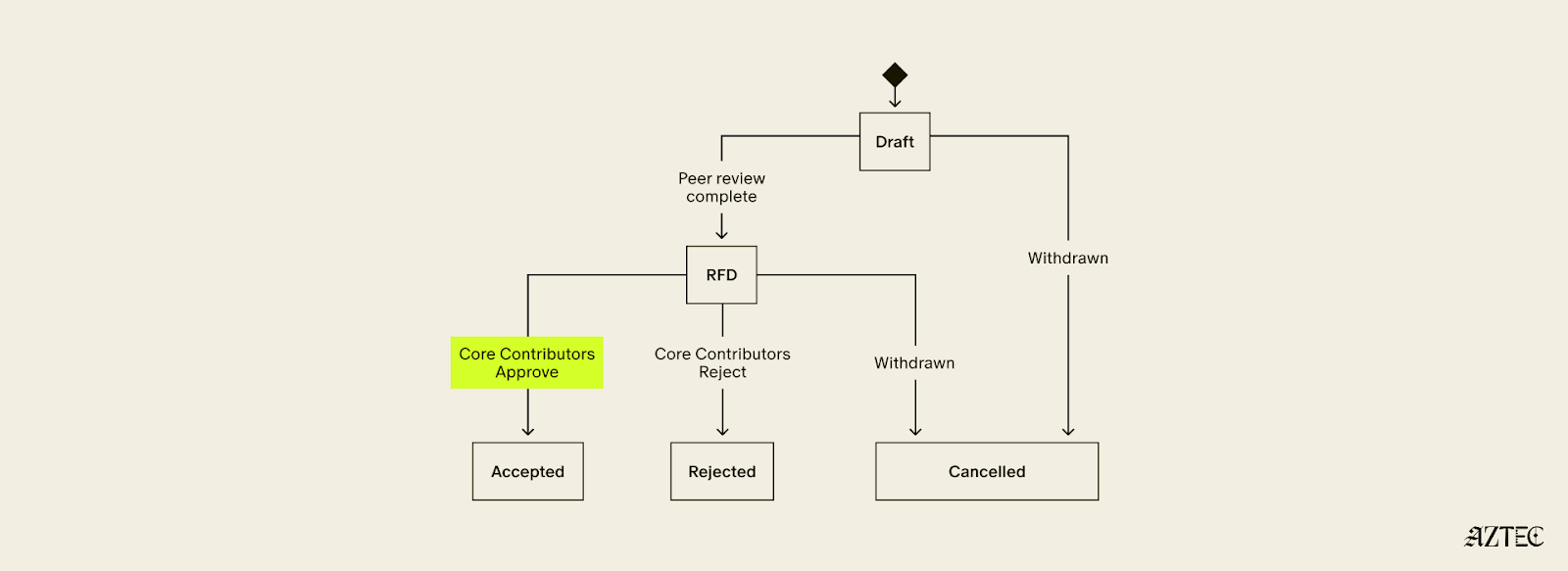
Once an AZIP is formalized as a pull request, it enters a structured lifecycle: Draft, Ready for Discussion, then Accepted or Rejected. Rejected AZIPs are not deleted — they remain permanently in the repository as a record of what was tried and why it was rejected. Nothing gets quietly buried.
Security Considerations are mandatory for all Core, Standard, and Economics AZIPs. Proposals without them cannot pass the Draft stage. Security is structural, not an afterthought.
Once Core Contributors, a merit-based and informal group of active protocol contributors, have reviewed an AZIP and approved it for inclusion, it gets bundled into an AZUP.
An AZUP takes everything an AZIP described and deploys it — a real smart contract, real onchain actions. Each AZUP includes a payload that encodes the exact onchain changes that will occur if the upgrade is approved. Anyone can inspect the payload on a block explorer and see precisely what will change before voting begins.
The payload then goes to sequencers for signaling. Sequencers are the backbone of the network. They propose blocks, attest to state, and serve as the first governance gate for any upgrade. A payload must accumulate enough signals from sequencers within a fixed round to advance. The people actually running the network have to express coordinated support before any change reaches a broader vote.
Once sequencers signal quorum, the proposal moves to tokenholders. Sequencers' staked voting power defaults to "yea" on proposals that came through the signaling path, meaning opposition must be active, not passive. Any sequencer or tokenholder who wants to vote against a proposal must explicitly re-delegate their stake before the voting snapshot is taken. The system rewards genuine engagement from all sides.
For a proposal to pass, it must meet quorum, a supermajority margin, and a minimum participation threshold, all three. If any condition is unmet, the proposal fails.
Even after a proposal passes, it does not execute immediately. A mandatory delay gives node operators time to deploy updated software, allows the community to perform final checks, and reduces the risk of sudden uncoordinated changes hitting the network. If the proposal is not executed within its grace period, it expires.
Failed AZUPs cannot be resubmitted. A new proposal must be created that directly addresses the feedback received. There is no way to simply retry and hope for a different result.
The teams building the network have no special governance power. Sequencers, tokenholders, and Core Contributors are the governing actors, each playing a distinct and non-redundant role.
No single party can force or block an upgrade. Sequencers can withhold signals. Tokenholders can vote nay. Proposals not executed within the grace period expire on their own.
This is decentralization working as intended. The network upgrades not because a team decides it should, but because the people running it agree that it should.
If you want to help shape what Aztec becomes, the forum is open. The proposals are public. The town square is yours.
Follow Aztec on X to stay up to date on the latest developments.
Aztec is novel code — the bleeding edge of cryptography and blockchain technology. As the first decentralized L2 on Ethereum, Aztec is powered by a global network of sequencers and provers. Decentralization introduces some novel challenges in how security is addressed; there is no centralized sequencer to pause or a centralized entity who has power over the network. The rollout of the network reflects this, with distinct goals at each phase.
Ignition
Validate governance and decentralized block building work as intended on Ethereum Mainnet.
Alpha
Enable transactions at 1TPS, ~6s block times and improve the security of the network via continual ongoing audits and bug bounty. New releases of the alpha network are expected regularly to address any security vulnerabilities. Please note, every alpha deployment is distinct and state is not migrated between Alpha releases.
Beta
We will transition to Beta once the network scales to >10 TPS, with reduced block times while ensuring 99.9% uptime. Additionally, the transition requires no critical bugs disclosed via bug bounty in 3 months. State migrations across network releases can be considered.
TL;DR: The roadmap from Ignition to Alpha to Beta is designed to reflect the core team's growing confidence in the network's security.
This phased approach lets us balance ecosystem growth while building security confidence and steadily expanding the community of researchers and tools working to validate the network’s security, soundness and correctness.
.png)
Ultimately, time in production without an exploit is the most reliable indicator of how secure a codebase is.
At the start of Alpha, that confidence is still developing. The core team believes the network is secure enough to support early ecosystem use cases and handle small amounts of value. However this is experimental alpha software and users should not deposit more value than they are willing to lose. Apps may choose to limit deposit amounts to mitigate risk for users.
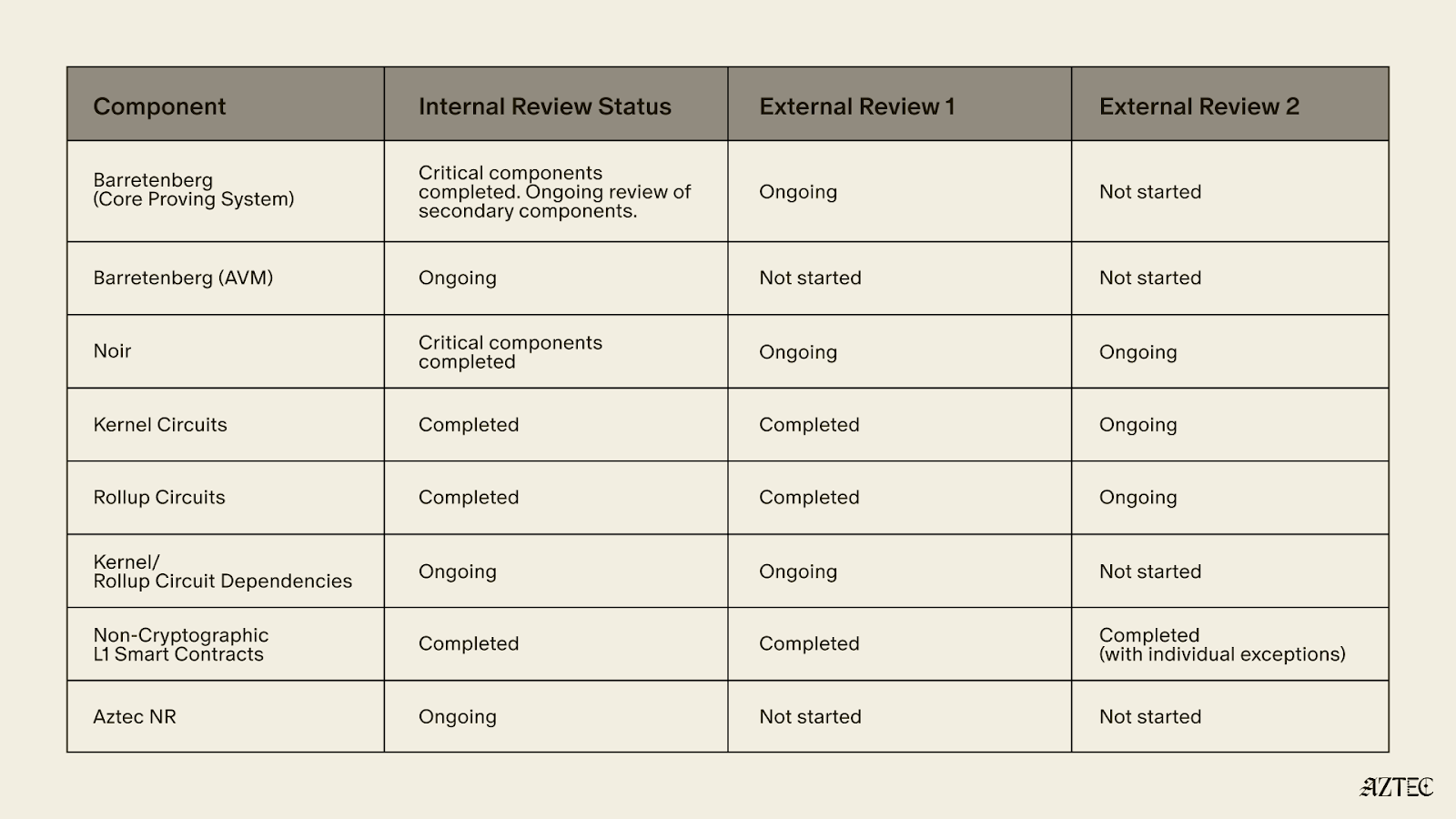
Audits are ongoing throughout Alpha, with the goal to achieve dual external audits across the entire codebase.
The table below shows current security and audit coverage at the time of writing.
The main bug bounty for the network is not yet live, other than for the non-cryptographic L1 smart contracts as audits are ongoing. We encourage security researchers to responsibly disclose findings in line with our security policy .
As the audits are still ongoing, we expect to discover vulnerabilities in various components. The fixes will be packaged and distributed with the “v5” release.
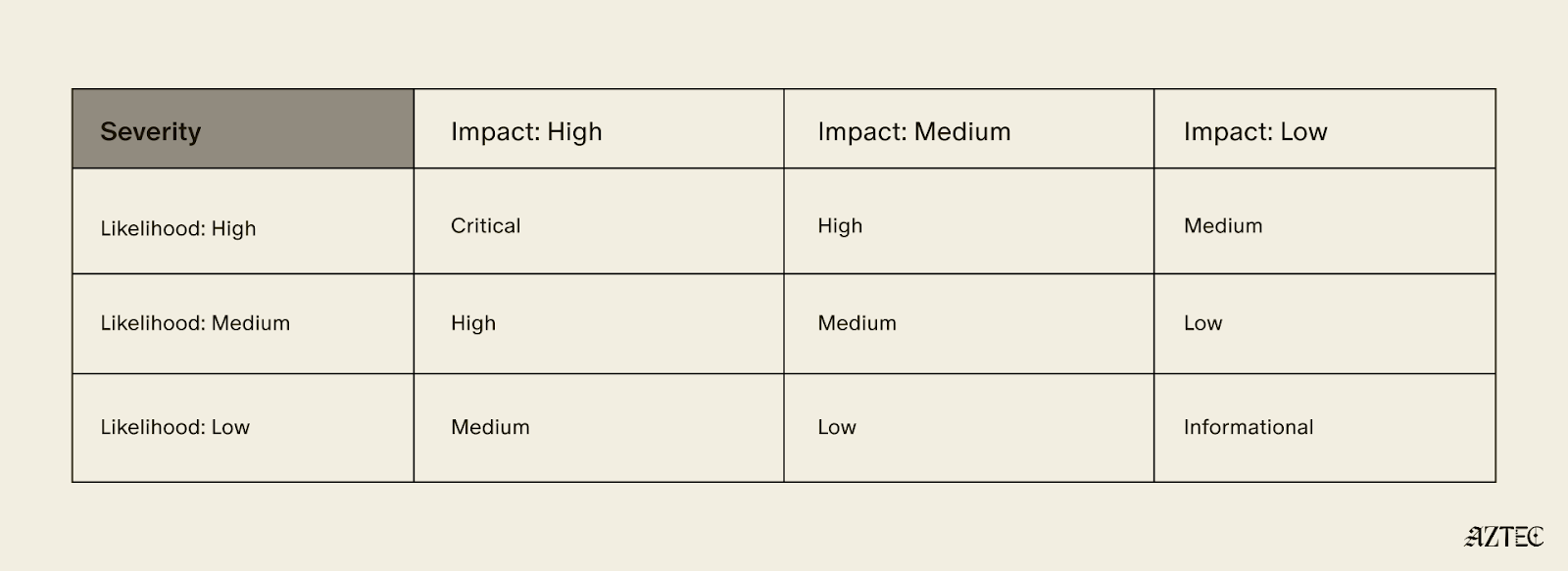
If we discover a Critical vulnerability in “v4” in accordance with the following severity matrix, which would require the change of verification keys to fix, we will first alert the portal operators to pause deposits and then post a message on the forum, stating that the rollup has a vulnerability.
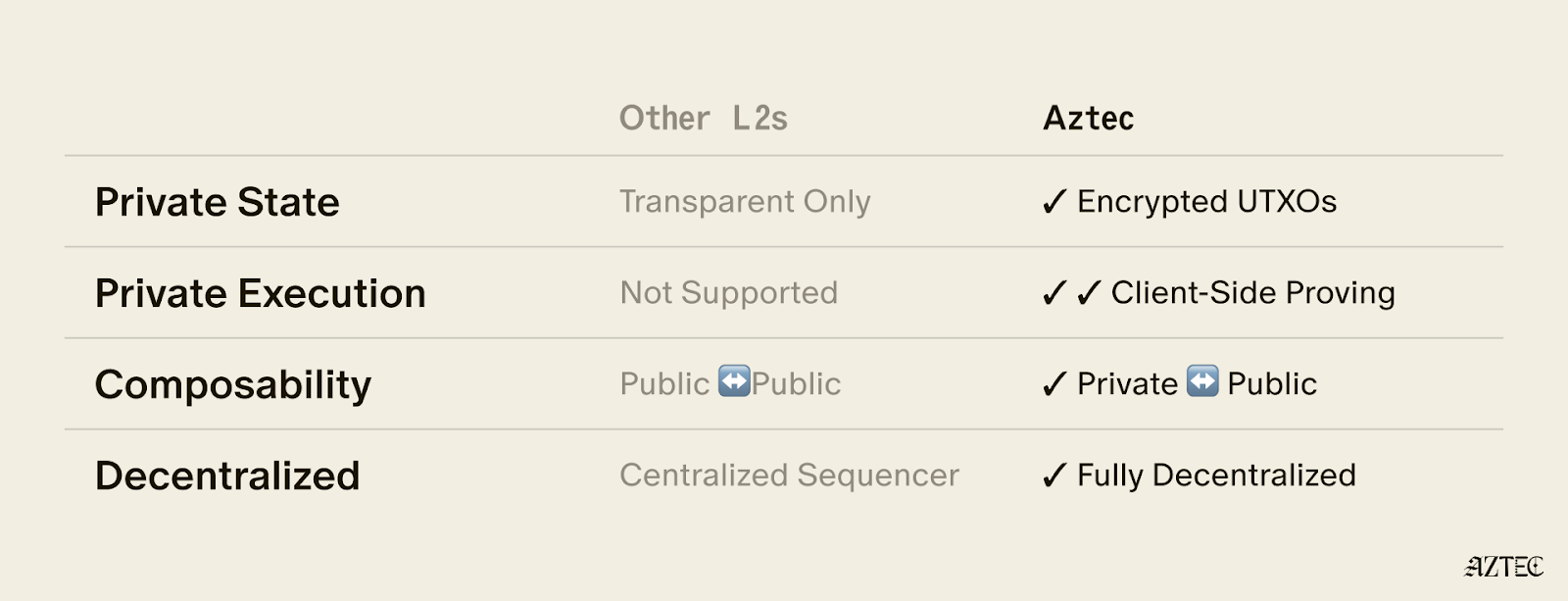
Aztec uses a hybrid execution model, handling private and public execution separately — and the security considerations differ between them.
As per the audit table above, it is clear that the Aztec Virtual Machine (AVM) has not yet completed its internal and external audits. This is intentional as all AVM execution is public, which allows it to benefit from a “Training Wheel” — the validator re-execution committee.
Every 72 seconds, a collection of newly proposed Aztec blocks are bundled into a "checkpoint" and submitted to L1. With each proposed checkpoint, a committee of 48 staking validators randomly selected from the entire set of validators (presently 3,959) re-execute all txs of all blocks in the checkpoint, and attest to the resulting state roots. 33 out of 48 attestations are required for the checkpoint proposal to be considered valid. The committee and the eventual zk proof must agree on the resultant state root for a checkpoint to be added to the proven chain. As a result, an attacker must control 33/48 of any given committee to exploit any bug in the AVM.
The only time the re-execution committee is not active is during the escape hatch, where the cost to propose a block is set at a level which attempts to quantify the security of the execution training wheel. For this version of the alpha network, this is set a 332M AZTEC, a figure intended to approximate the economic protection the committee normally provides, equivalent to roughly 19% of the un-staked circulating supply at the time of writing. Since the Aztec Foundation holds a significant portion of that supply, the effective threshold is considerably higher in practice.
A key design assumption is that just-in-time bribery of the sequencer committee is impractical and the only ****realistic attack vector is stake acquisition, not bribery.
Assuming a sequencer set size of 4,000 and a committee that rotates each epoch (~38.4mins) from the full sequencer set using a Fisher-Yates shuffle seeded by L1 RANDAO we can see the probability and amount of stake required in the table below.
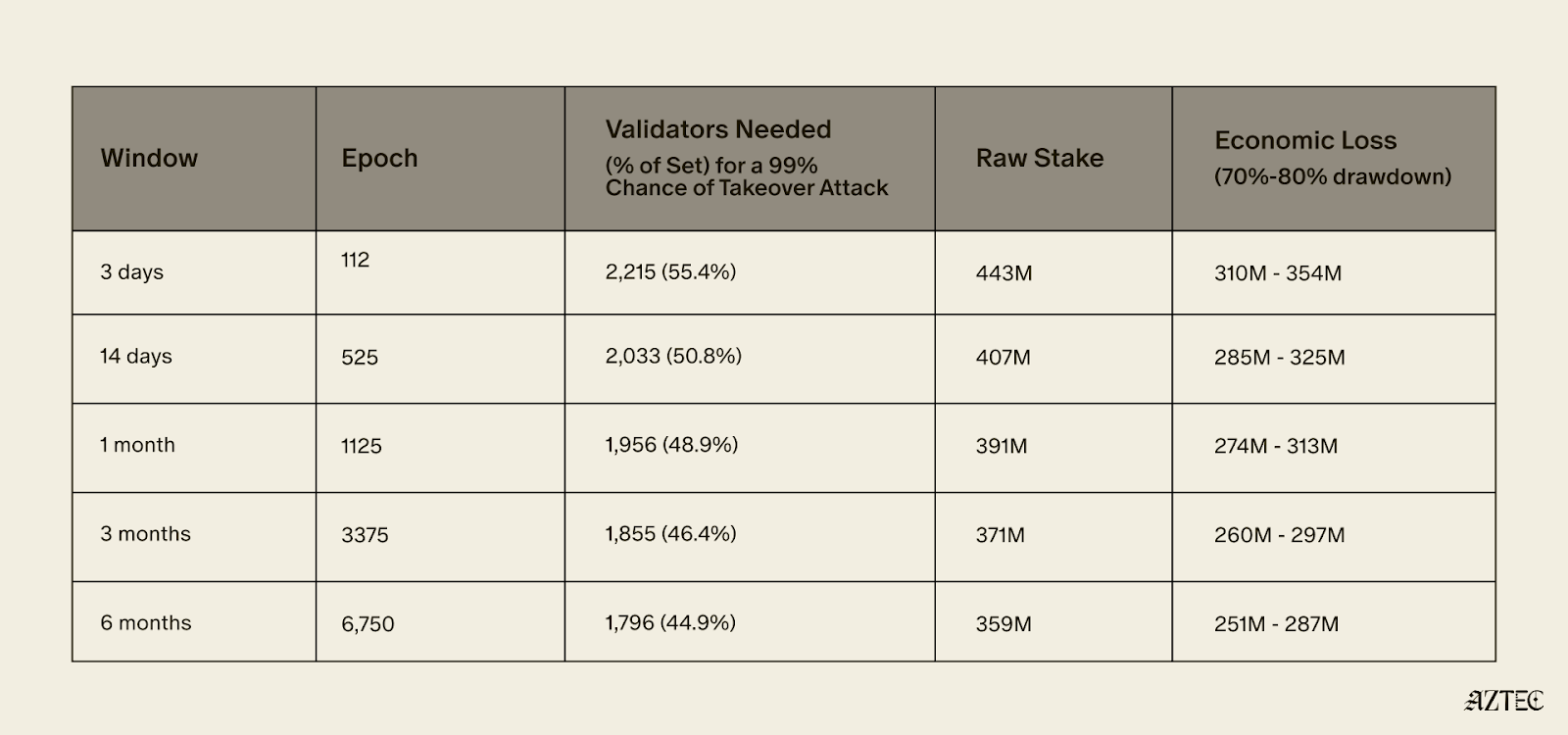
To achieve a 99% probability of controlling at least one supermajority within 3 days, an attacker would need to control approximately 55.4% of the validator set - roughly 2,215 sequencers representing 443M AZTEC in stake. Assuming an exploit is successful their stake would likely de-value by 70-80%, resulting in an expected economic loss of approximately 332M AZTEC.
To achieve only a 0.5% probability of controlling at least one supermajority within 6 months, an attacker would need to control approximately 33.88% of the validator set.
The practical effect of this training wheel is that the network can exist while there are known security issues with the AVM, as long as the value an attacker would gain from any potential exploit is less than the cost of acquiring 332M AZTEC.
The training wheel allows security researchers to spend more time on the private execution paths that don’t benefit from the training wheel and for the network to be deployed in an alpha version where security researchers can attempt to find additional AVM exploits.
In concrete terms, the training wheel means the Alpha network can reasonably secure value up to around 332M AZTEC (~$6.5M at the time of writing).
Ecosystem builders should keep the above limits in mind, particularly when designing portal contracts that bridge funds into the network.
Portals are the main way value will be bridged into the alpha network, and as a result are also the main target for any exploits. The design of portals can allow the network to secure far higher value. If a portal secures > 332M AZTEC and allows all of its funds to be taken in one withdrawal without any rate limits, delays or pause functionality then it is a target for an AVM exploit attack.
If a portal implements a maximum withdrawal per user, pause functionality or delays for larger withdrawals it becomes harder for an attacker to steal a large quantum of funds in one go.
The Aztec Alpha code is ready to go. The next step is for someone in the community to submit a governance proposal and for the network to vote on enabling transactions. This is decentralization working as intended.
Once live, Alpha will run at 1 TPS with roughly 6 second block times. Audits are still ongoing across several components, so keep deposits small and only put in what you're comfortable losing.
On the security side, a 48-validator re-execution committee provides the main protection during Alpha, requiring 33/48 consensus on every 72-second checkpoint. Successfully attacking the AVM would require controlling roughly 55% of the validator set at a cost of around 332M AZTEC, putting the practical security ceiling at approximately $6.5M.
Alpha is about growing the ecosystem, expanding the security of the network, and accumulating the one thing no audit can shortcut: time in production. This is the network maturing in exactly the way it was designed to as it progresses toward Beta.
The Ignition Chain launched late last year, as the first fully decentralized L2 on Ethereum– a huge milestone for decentralized networks. The team has reinvented what true programmable privacy means, building the execution model from the ground up— combining the programmability of Ethereum with the privacy of Zcash in a single execution environment.
Since then, the network has been running with zero downtime with 3,500+ sequencers and 50+ provers across five continents. With the infrastructure now in place, the network is fully in the hands of the community, and the culmination of the past 8 years of work is now converging.
Major upgrades have landed across four tracks: the execution layer, the proving system, the programming language, Noir, and the decentralization stack. Together, these milestones deliver on Aztec’s original promise, a system where developers can write fully programmable smart contracts with customizable privacy.
The infrastructure is in place. The code is ready. And we’re ready to ship.
The execution layer delivers on Aztec's core promise: fully programmable, privacy-preserving smart contracts on Ethereum.
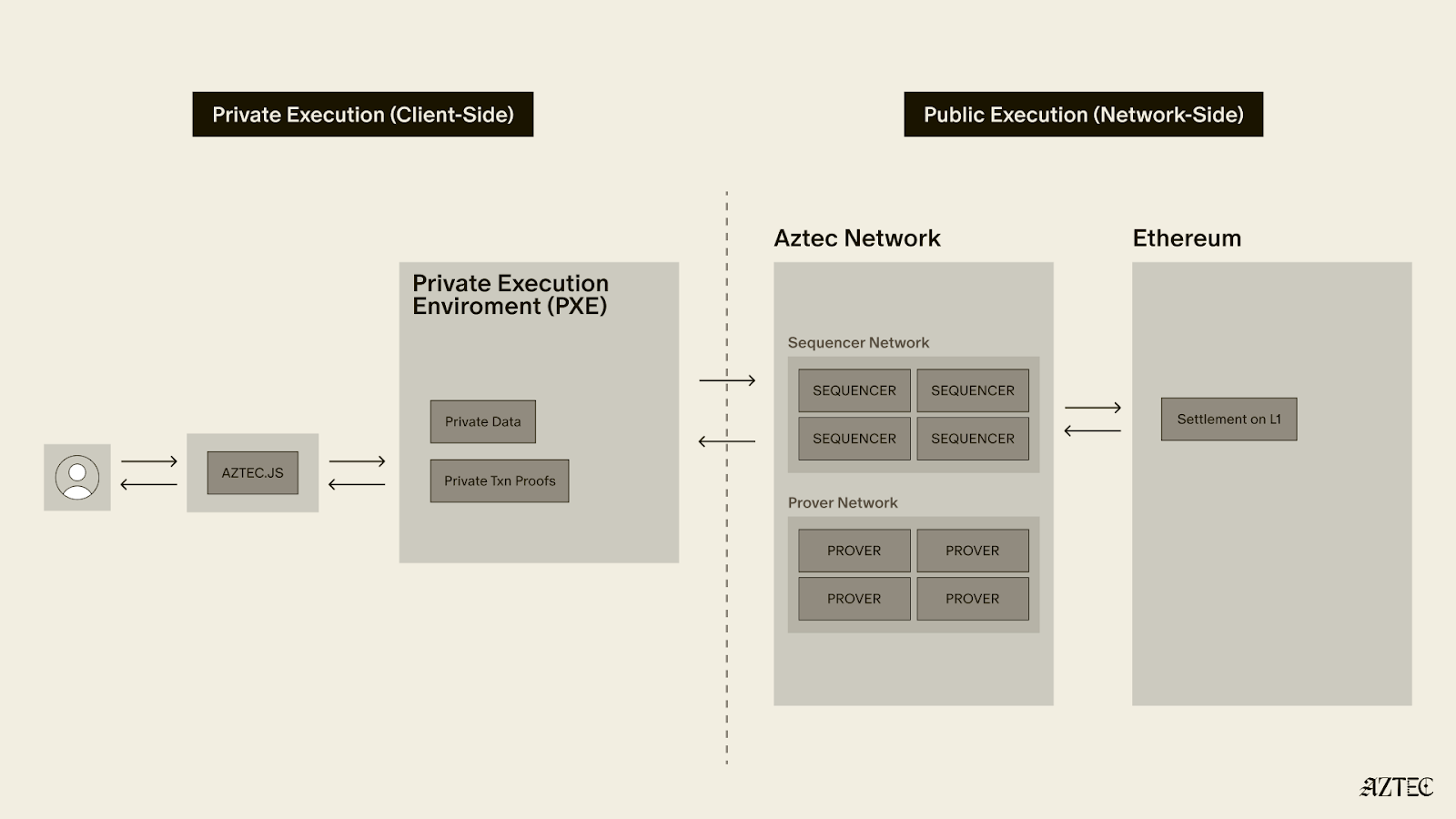
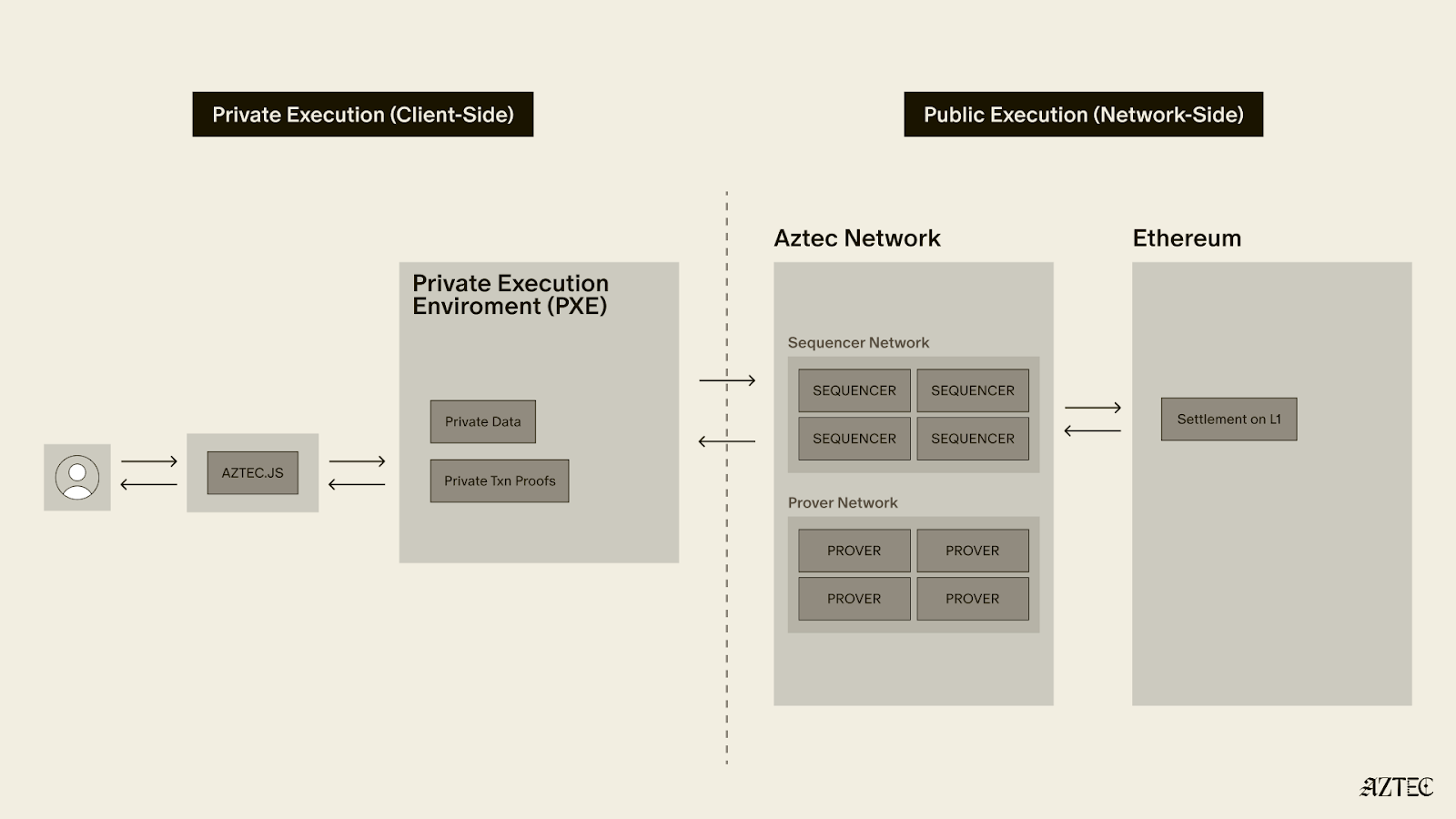
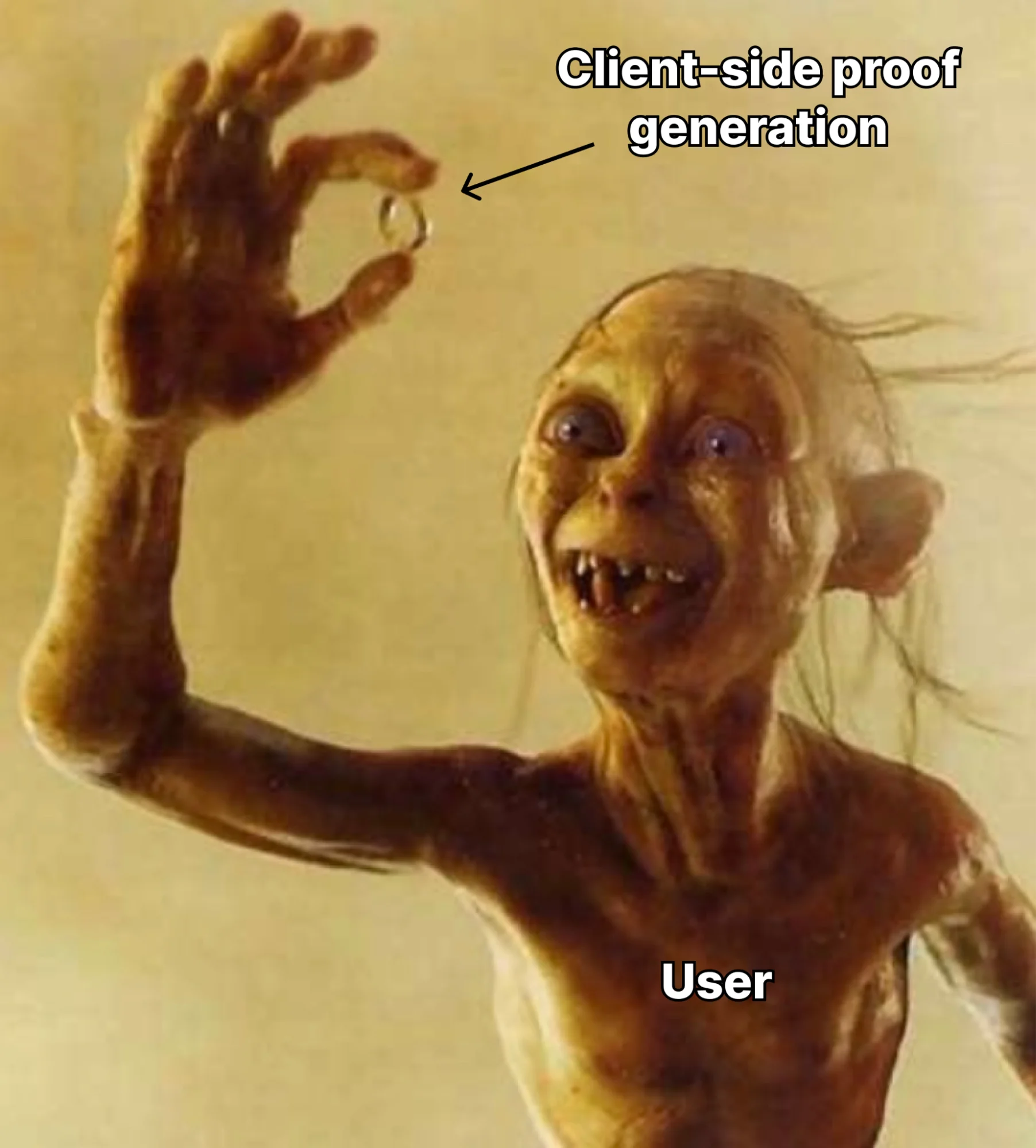
A complete dual state model is now in place–with both private and public state. Private functions execute client-side in the Private Execution Environment (PXE), running directly in the user's browser and generating zero-knowledge proofs locally, so that private data never leaves the original device. Public functions execute on the Aztec Virtual Machine (AVM) on the network side.
Aztec.js is now live, giving developers a full SDK for managing accounts and interacting with contracts. Native account abstraction has been implemented, meaning every account is a smart contract with customizable authentication rules. Note discovery has been solved through a tagging mechanism, allowing recipients to efficiently query for relevant notes without downloading and decrypting everything on the network.
Contract standards are underway, with the Wonderland team delivering AIP-20 for tokens and AIP-721 for NFTs, along with escrow contracts and logic libraries, providing the production-ready building blocks for the Alpha Network.
The proving system is what makes Aztec's privacy guarantees real, and it has deep roots.
In 2019, Aztec's cofounder Zac Williamson and Chief Scientist Ariel Gabizon introduced PLONK, which became one of the most widely used proving systems in zero-knowledge cryptography. Since then, Aztec's cryptographic backend, Barretenberg, has evolved through multiple generations, each facilitating faster, lighter, and more efficient proving than the last. The latest innovation, CHONK (Client-side Highly Optimized ploNK), is purpose-built for proving on phones and browsers and is what powers proof generation for the Alpha Network.
CHONK is a major leap forward for the user experience, dramatically reducing the memory and time required to generate proofs on consumer devices. It leverages best-in-class circuit primitives, a HyperNova-style folding scheme for efficiently processing chains of private function calls, and Goblin, a hyper-efficient purpose-built recursion acceleration scheme. The result is that private transactions can be proven on the devices people actually use, not just powerful servers.
This matters because privacy on Aztec means proofs are generated on the user's own device, keeping private data private. If proving is too slow or too resource-intensive, privacy becomes impractical. CHONK makes it practical.
Decentralization is what makes Aztec's privacy guarantees credible. Without it, a central operator could censor transactions, introduce backdoors, or compromise user privacy at will.
Aztec addressed this by hardcoding decentralized sequencing, proving, and governance directly into the base protocol. The Ignition Chain has proven the stability of this consensus layer, maintaining zero downtime with over 3,500 sequencers and 50+ provers running across five continents. Aztec Labs and the Aztec Foundation run no sequencers and do not participate in governance.
Noir 1.0 is nearing completion, bringing a stable, production-grade language within reach. Aztec's own protocol circuits have been entirely rewritten in Noir, meaning the language is already battle-tested at the deepest layer of the stack.
Internal and external audits of the compiler and toolchain are progressing in parallel, and security tooling including fuzzers and bytecode parsers is nearly finished. A stable, audited language means application teams can build on Alpha with confidence that the foundation beneath them won't shift.
The code for Alpha Network, a functionally complete and raw version of the network, is ready.
The Alpha Network brings fully programmable, privacy-preserving smart contracts to Ethereum for the first time. It's the culmination of years of parallel work across the four tracks in the Aztec Roadmap. Together, they enable efficient client-side proofs that power customizable smart contracts, letting users choose exactly what stays private and what goes public.
No other project in the space is close to shipping this.
The code is written. The network is running. All the pieces are in place. The governance proposal is now live on the forum and open for discussion. Read through it, ask questions, poke holes, and help shape the path forward.
Once the community is aligned, the proposal moves to a vote. This is how a decentralized network upgrades. Not by a team pushing a button, but by the people running it.
Programmable privacy will unlock a renaissance in onchain adoption. Real-world applications are coming and institutions are paying attention. Alpha represents the culmination of eight years of intense work to deliver privacy on Ethereum.
Now it needs to be battle-tested in the wild.
View the updated product roadmap here and join us on Thursday, March 5th, at 3 pm UTC on X to hear more about the most recent updates to our product roadmap.
Alpha is live: a fully feature-complete, privacy-first network. The infrastructure is in place, privacy is native to the protocol, and developers can now build truly private applications.
Nine years ago, we set out to redesign blockchain for privacy. The goal: create a system institutions can adopt while giving users true control of their digital lives. Privacy band-aids are coming to Ethereum (someday), but it’s clear we need privacy now, and there’s an arms race underway to build it. Privacy is complex, it’s not a feature you can bolt-on as an afterthought. It demands a ground-up approach, deep tech stack integration, and complete decentralization.
In November 2025, the Aztec Ignition Chain went live as the first decentralized L2 on Ethereum, it’s the coordination layer that the execution layer sits on top of. The network is not operated by the Aztec Labs or the Aztec Foundation, it’s run by the community, making it the true backbone of Aztec.
With the infrastructure in place and a unanimous community vote, the network enters Alpha.
Alpha is the first Layer 2 with a full execution environment for private smart contracts. All accounts, transactions, and the execution itself can be completely private. Developers can now choose what they want public and what they want to keep private while building with the three privacy pillars we have in place across data, identity, and compute.
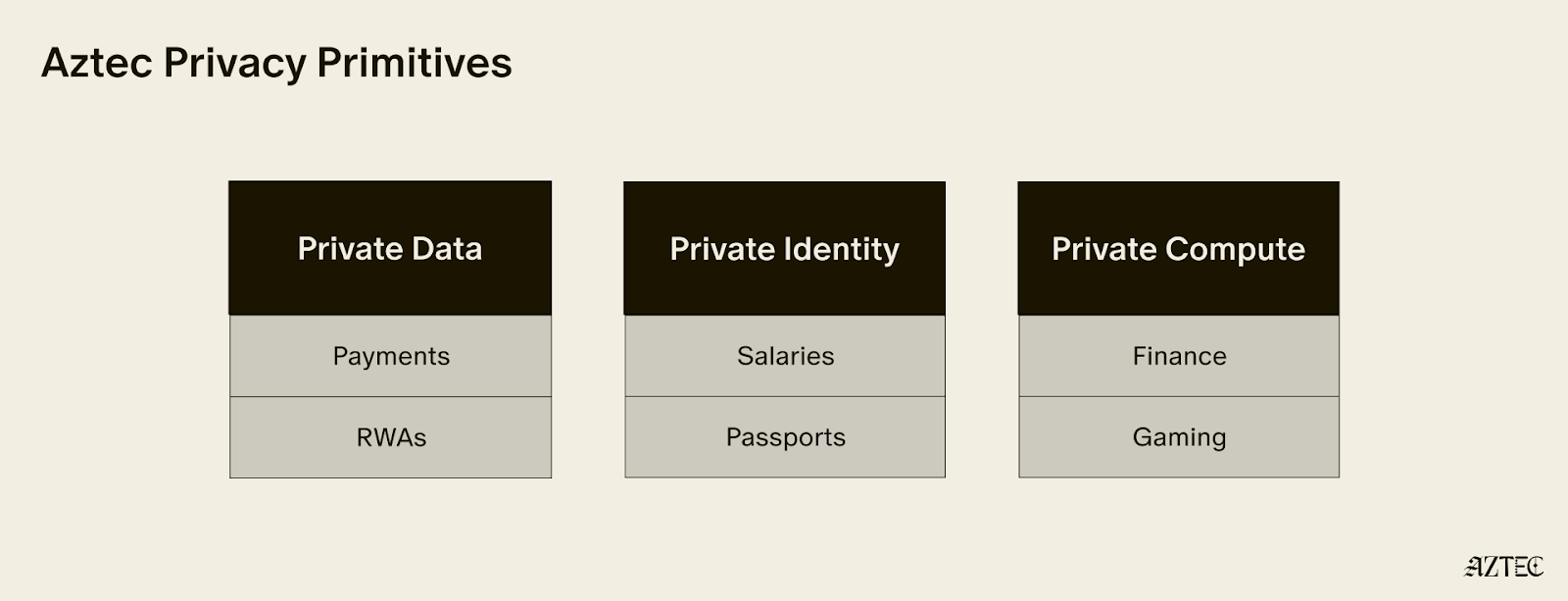
These privacy pillars, which can be used individually or combined, break down into three core layers:
Alpha is feature complete–meaning this is the only full-stack solution for adding privacy to your business or application. You build, and Aztec handles the cryptography under the hood.
It’s Composable. Private-preserving contracts are not isolated; they can talk to each other and seamlessly blend both private and public state across contracts. Privacy can be preserved across contract calls for full callstack privacy.
No backdoor access. Aztec is the only decentralized L2, and is launching as a fully decentralized rollup with a Layer 1 escape hatch.
It’s Compliant. Companies are missing out on the benefits of blockchains because transparent chains expose user data, while private networks protect it, but still offer fully customizable controls. Now they can build compliant apps that move value around the world instantly.
Developers can explore our privacy primitives across data, identity, and compute and start building with them using the documentation here. Note that this is an early version of the network with known vulnerabilities, see this post for details. While this is the first iteration of the network, there will be several upgrades that secure and harden the network on our path to Beta. If you’d like to learn more about how you can integrate privacy into your project, reach out here.
To hear directly from our Cofounders, join our live from Cannes Q&A on Tuesday, March 31st at 9:30 am ET. Follow us on X to get the latest updates from the Aztec Network.
The Ignition Chain launched late last year, as the first fully decentralized L2 on Ethereum– a huge milestone for decentralized networks. The team has reinvented what true programmable privacy means, building the execution model from the ground up— combining the programmability of Ethereum with the privacy of Zcash in a single execution environment.
Since then, the network has been running with zero downtime with 3,500+ sequencers and 50+ provers across five continents. With the infrastructure now in place, the network is fully in the hands of the community, and the culmination of the past 8 years of work is now converging.
Major upgrades have landed across four tracks: the execution layer, the proving system, the programming language, Noir, and the decentralization stack. Together, these milestones deliver on Aztec’s original promise, a system where developers can write fully programmable smart contracts with customizable privacy.
The infrastructure is in place. The code is ready. And we’re ready to ship.
The execution layer delivers on Aztec's core promise: fully programmable, privacy-preserving smart contracts on Ethereum.
A complete dual state model is now in place–with both private and public state. Private functions execute client-side in the Private Execution Environment (PXE), running directly in the user's browser and generating zero-knowledge proofs locally, so that private data never leaves the original device. Public functions execute on the Aztec Virtual Machine (AVM) on the network side.
Aztec.js is now live, giving developers a full SDK for managing accounts and interacting with contracts. Native account abstraction has been implemented, meaning every account is a smart contract with customizable authentication rules. Note discovery has been solved through a tagging mechanism, allowing recipients to efficiently query for relevant notes without downloading and decrypting everything on the network.
Contract standards are underway, with the Wonderland team delivering AIP-20 for tokens and AIP-721 for NFTs, along with escrow contracts and logic libraries, providing the production-ready building blocks for the Alpha Network.
The proving system is what makes Aztec's privacy guarantees real, and it has deep roots.
In 2019, Aztec's cofounder Zac Williamson and Chief Scientist Ariel Gabizon introduced PLONK, which became one of the most widely used proving systems in zero-knowledge cryptography. Since then, Aztec's cryptographic backend, Barretenberg, has evolved through multiple generations, each facilitating faster, lighter, and more efficient proving than the last. The latest innovation, CHONK (Client-side Highly Optimized ploNK), is purpose-built for proving on phones and browsers and is what powers proof generation for the Alpha Network.
CHONK is a major leap forward for the user experience, dramatically reducing the memory and time required to generate proofs on consumer devices. It leverages best-in-class circuit primitives, a HyperNova-style folding scheme for efficiently processing chains of private function calls, and Goblin, a hyper-efficient purpose-built recursion acceleration scheme. The result is that private transactions can be proven on the devices people actually use, not just powerful servers.
This matters because privacy on Aztec means proofs are generated on the user's own device, keeping private data private. If proving is too slow or too resource-intensive, privacy becomes impractical. CHONK makes it practical.
Decentralization is what makes Aztec's privacy guarantees credible. Without it, a central operator could censor transactions, introduce backdoors, or compromise user privacy at will.
Aztec addressed this by hardcoding decentralized sequencing, proving, and governance directly into the base protocol. The Ignition Chain has proven the stability of this consensus layer, maintaining zero downtime with over 3,500 sequencers and 50+ provers running across five continents. Aztec Labs and the Aztec Foundation run no sequencers and do not participate in governance.
Noir 1.0 is nearing completion, bringing a stable, production-grade language within reach. Aztec's own protocol circuits have been entirely rewritten in Noir, meaning the language is already battle-tested at the deepest layer of the stack.
Internal and external audits of the compiler and toolchain are progressing in parallel, and security tooling including fuzzers and bytecode parsers is nearly finished. A stable, audited language means application teams can build on Alpha with confidence that the foundation beneath them won't shift.
The code for Alpha Network, a functionally complete and raw version of the network, is ready.
The Alpha Network brings fully programmable, privacy-preserving smart contracts to Ethereum for the first time. It's the culmination of years of parallel work across the four tracks in the Aztec Roadmap. Together, they enable efficient client-side proofs that power customizable smart contracts, letting users choose exactly what stays private and what goes public.
No other project in the space is close to shipping this.
The code is written. The network is running. All the pieces are in place. The governance proposal is now live on the forum and open for discussion. Read through it, ask questions, poke holes, and help shape the path forward.
Once the community is aligned, the proposal moves to a vote. This is how a decentralized network upgrades. Not by a team pushing a button, but by the people running it.
Programmable privacy will unlock a renaissance in onchain adoption. Real-world applications are coming and institutions are paying attention. Alpha represents the culmination of eight years of intense work to deliver privacy on Ethereum.
Now it needs to be battle-tested in the wild.
View the updated product roadmap here and join us on Thursday, March 5th, at 3 pm UTC on X to hear more about the most recent updates to our product roadmap.
Privacy has emerged as a major driver for the crypto industry in 2025. We’ve seen the explosion of Zcash, the Ethereum Foundation’s refocusing of PSE, and the launch of Aztec’s testnet with over 24,000 validators powering the network. Many apps have also emerged to bring private transactions to Ethereum and Solana in various ways, and exciting technologies like ZKPassport that privately bring identity on-chain using Noir have become some of the most talked about developments for ushering in the next big movements to the space.
Underpinning all of these developments is the emerging consensus that without privacy, blockchains will struggle to gain real-world adoption.
Without privacy, institutions can’t bring assets on-chain in a compliant way or conduct complex swaps and trades without revealing their strategies. Without privacy, DeFi remains dominated and controlled by advanced traders who can see all upcoming transactions and manipulate the market. Without privacy, regular people will not want to move their lives on-chain for the entire world to see every detail about their every move.
While there's been lots of talk about privacy, few can define it. In this piece we’ll outline the three pillars of privacy and gives you a framework for evaluating the privacy claims of any project.
True privacy rests on three essential pillars: transaction privacy, identity privacy, and computational privacy. It is only when we have all three pillars that we see the emergence of a private world computer.
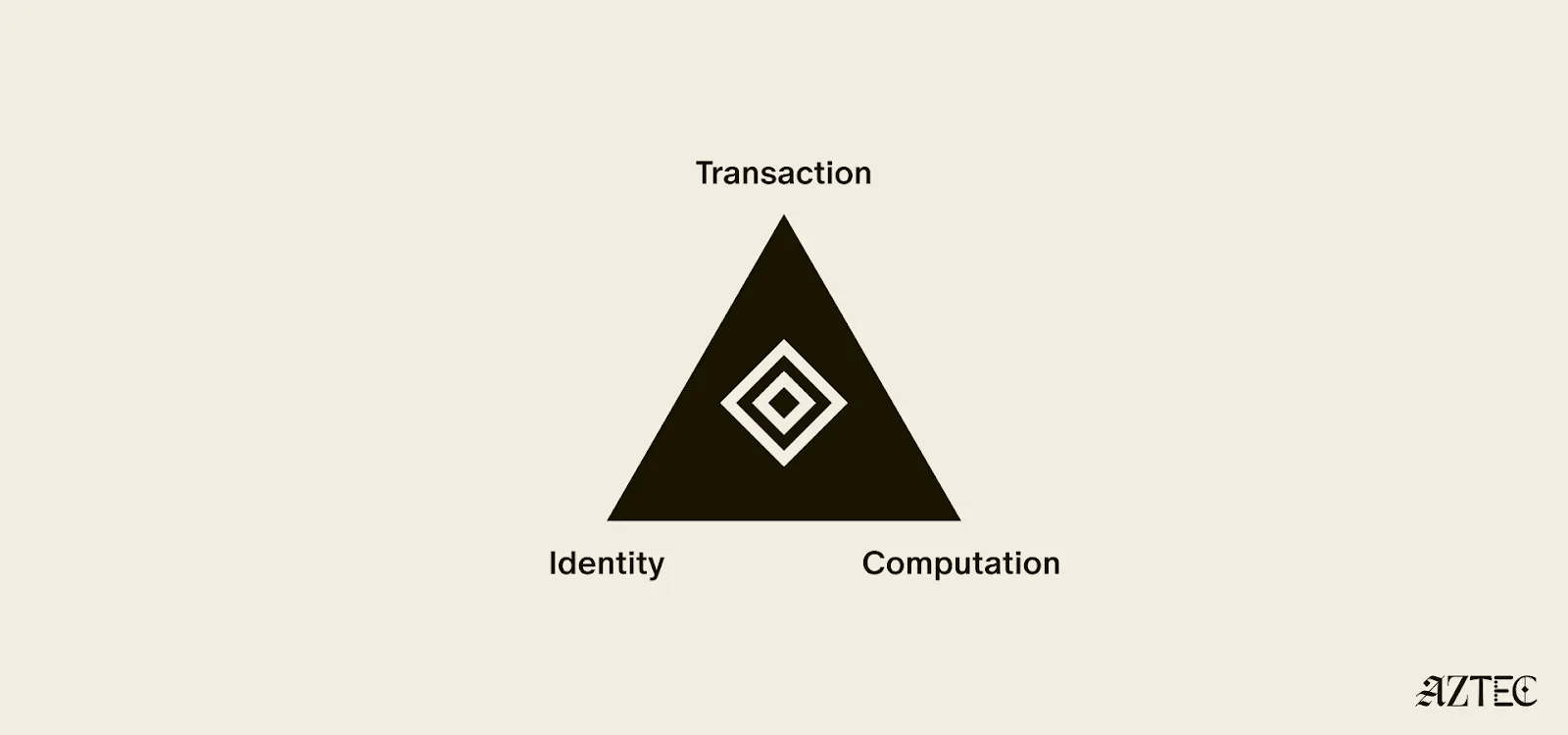
Transaction privacy means that both inputs and outputs are not viewable by anyone other than the intended participants. Inputs include any asset, value, message, or function calldata that is being sent. Outputs include any state changes or transaction effects, or any transaction metadata caused by the transaction. Transaction privacy is often primarily achieved using a UTXO model (like Zcash or Aztec’s private state tree). If a project has only the option for this pillar, it can be said to be confidential, but not private.
Identity privacy means that the identities of those involved are not viewable by anyone other than the intended participants. This includes addresses or accounts and any information about the identity of the participants, such as tx.origin, msg.sender, or linking one’s private account to public accounts. Identity privacy can be achieved in several ways, including client-side proof generation that keeps all user info on the users’ devices. If a project has only the option for this pillar, it can be said to be anonymous, but not private.
Computation privacy means that any activity that happens is not viewable by anyone other than the intended participants. This includes the contract code itself, function execution, contract address, and full callstack privacy. Additionally, any metadata generated by the transaction is able to be appropriately obfuscated (such as transaction effects, events are appropriately padded, inclusion block number are in appropriate sets). Callstack privacy includes which contracts you call, what functions in those contracts you’ve called, what the results of those functions were, any subsequent functions that will be called after, and what the inputs to the function were. A project must have the option for this pillar to do anything privately other than basic transactions.
Bitcoin ushered in a new paradigm of digital money. As a permissionless, peer-to-peer currency and store of value, it changed the way value could be sent around the world and who could participate. Ethereum expanded this vision to bring us the world computer, a decentralized, general-purpose blockchain with programmable smart contracts.
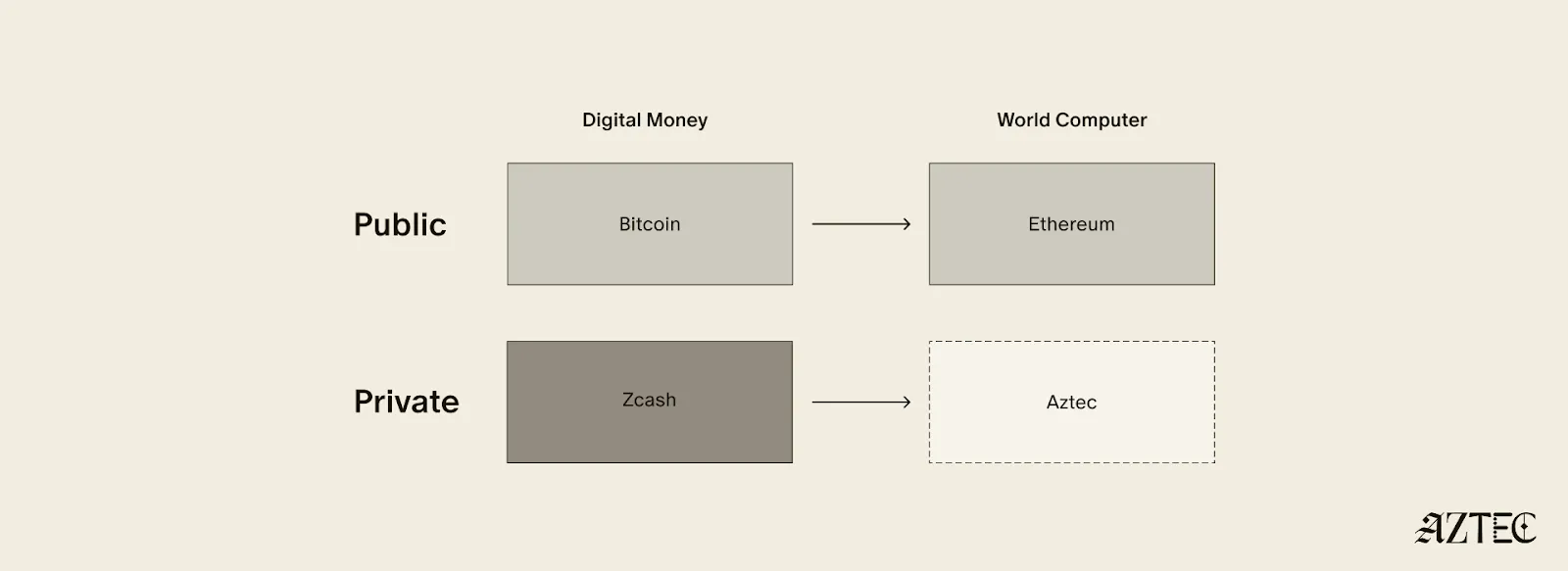
Given the limitations of running a transparent blockchain that exposes all user activity, accounts, and assets, it was clear that adding the option to preserve privacy would unlock many benefits (and more closely resemble real cash). But this was a very challenging problem. Zcash was one of the first to extend Bitcoin’s functionality with optional privacy, unlocking a new privacy-preserving UTXO model for transacting privately. As we’ll see below, many of the current privacy-focused projects are working on similar kinds of private digital money for Ethereum or other chains.
Now, Aztec is bringing us the final missing piece: a private world computer.
A private world computer is fully decentralized, programmable, and permissionless like Ethereum and has optional privacy at every level. In other words, Aztec is extending all the functionality of Ethereum with optional transaction, identity, and computational privacy. This is the only approach that enables fully compliant, decentralized applications to be built that preserve user privacy, a new design space that we see as ushering in the next Renaissance for the space.
Private digital money emerges when you have the first two privacy pillars covered - transactions and identity - but you don’t have the third - computation. Almost all projects today that claim some level of privacy are working on private digital money. This includes everything from privacy pools on Ethereum and L2s to newly emerging payment L1s like Tempo and Arc that are developing various degrees of transaction privacy
When it comes to digital money, privacy exists on a spectrum. If your identity is hidden but your transactions are visible, that's what we call anonymous. If your transactions are hidden but your identity is known, that's confidential. And when both your identity and transactions are protected, that's true privacy. Projects are working on many different approaches to implement this, from PSE to Payy using Noir, the zkDSL built to make it intuitive to build zk applications using familiar Rust-like syntax.
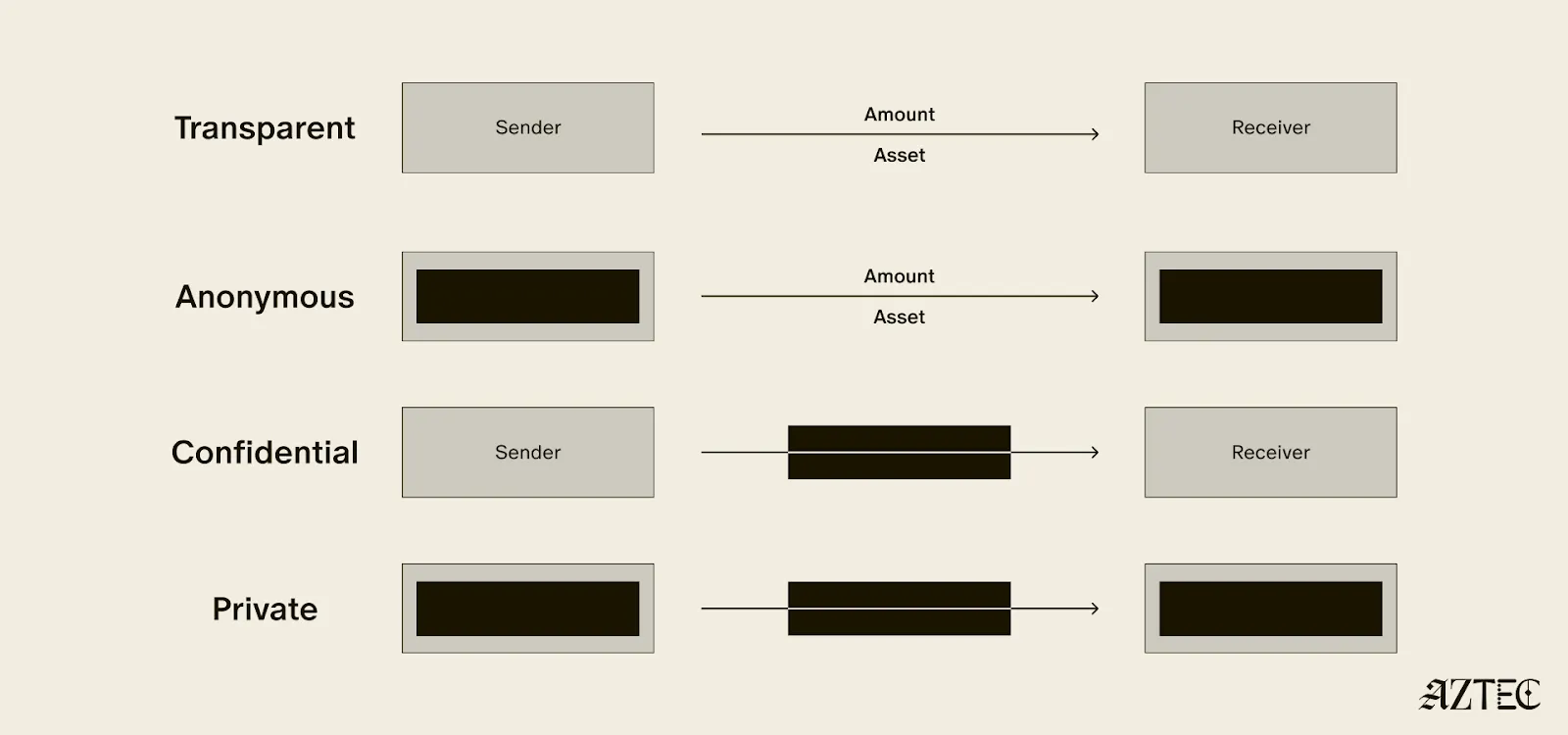
Private digital money is designed to make payments private, but any interaction with more complex smart contracts than a straightforward payment transaction is fully exposed.
What if we also want to build decentralized private apps using smart contracts (usually multiple that talk to each other)? For this, you need all three privacy pillars: transaction, identity, and compute.
If you have these three pillars covered and you have decentralization, you have built a private world computer. Without decentralization, you are vulnerable to censorship, privileged backdoors and inevitable centralized control that can compromise privacy guarantees.
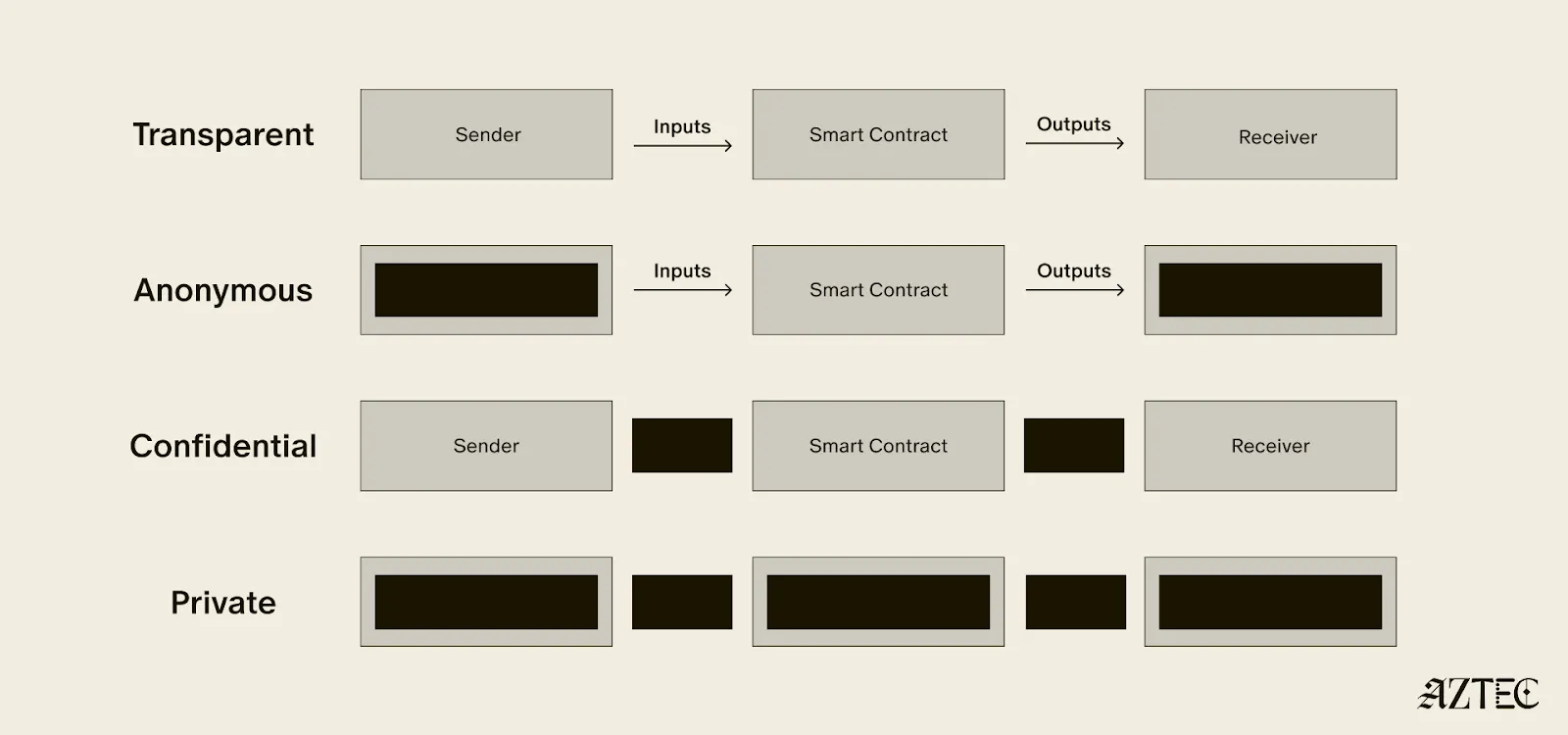
What exactly is a private world computer? A private world computer extends all the functionality of Ethereum with optional privacy at every level, so developers can easily control which aspects they want public or private and users can selectively disclose information. With Aztec, developers can build apps with optional transaction, identity, and compute privacy on a fully decentralized network. Below, we’ll break down the main components of a private world computer.
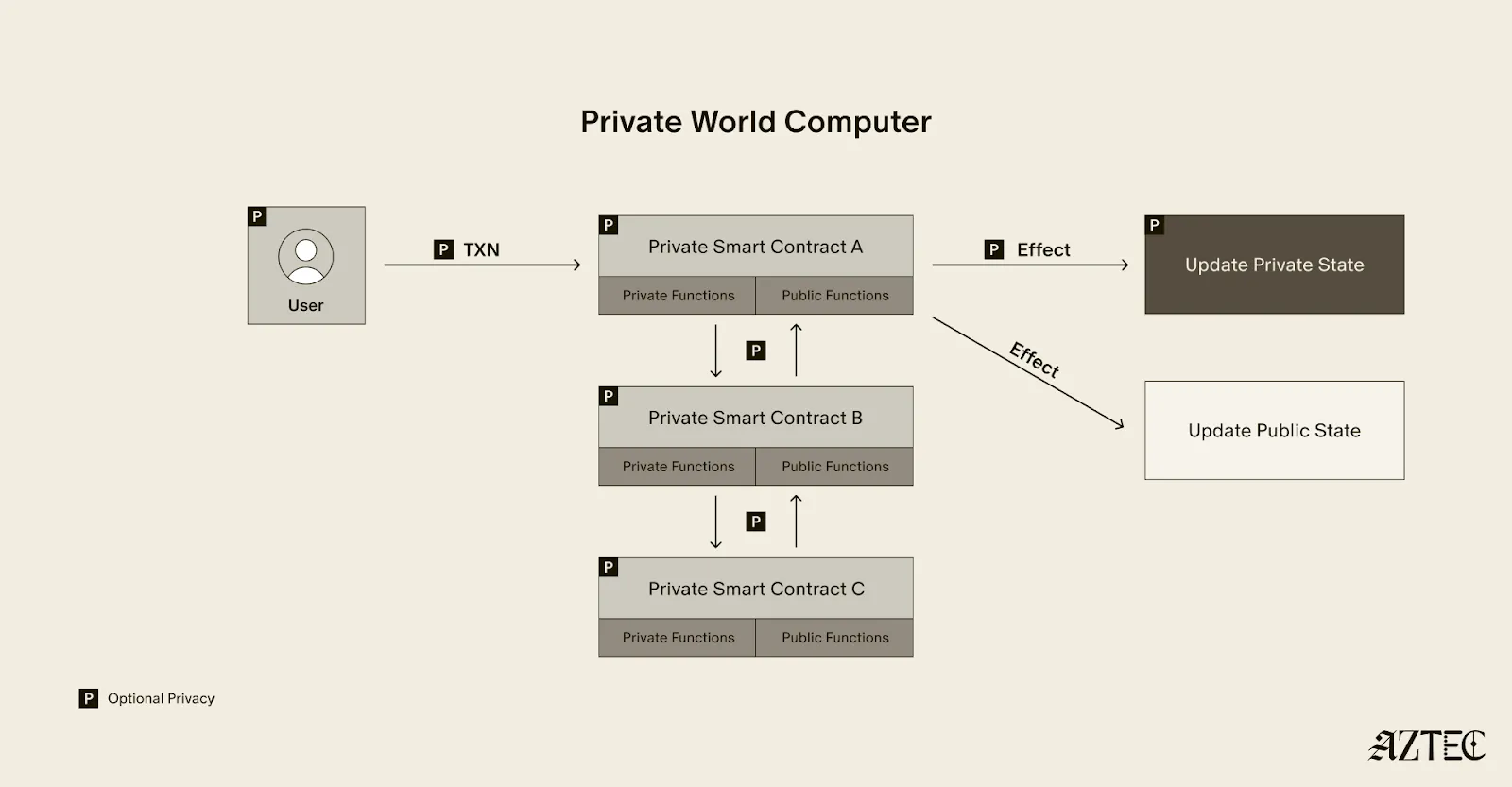
A private world computer is powered by private smart contracts. Private smart contracts have fully optional privacy and also enable seamless public and private function interaction.
Private smart contracts simply extend the functionality of regular smart contracts with added privacy.
As a developer, you can easily designate which functions you want to keep private and which you want to make public. For example, a voting app might allow users to privately cast votes and publicly display the result. Private smart contracts can also interact privately with other smart contracts, without needing to make it public which contracts have interacted.
Transaction: Aztec supports the optionality for fully private inputs, including messages, state, and function calldata. Private state is updated via a private UTXO state tree.
Identity: Using client-side proofs and function execution, Aztec can optionally keep all user info private, including tx.origin and msg.sender for transactions.
Computation: The contract code itself, function execution, and call stack can all be kept private. This includes which contracts you call, what functions in those contracts you’ve called, what the results of those functions were, and what the inputs to the function were.
A decentralized network must be made up of a permissionless network of operators who run the network and decide on upgrades. Aztec is run by a decentralized network of node operators who propose and attest to transactions. Rollup proofs on Aztec are also run by a decentralized prover network that can permissionlessly submit proofs and participate in block rewards. Finally, the Aztec network is governed by the sequencers, who propose, signal, vote, and execute network upgrades.
A private world computer enables the creation of DeFi applications where accounts, transactions, order books, and swaps remain private. Users can protect their trading strategies and positions from public view, preventing front-running and maintaining competitive advantages. Additionally, users can bridge privately into cross-chain DeFi applications, allowing them to participate in DeFi across multiple blockchains while keeping their identity private despite being on an existing transparent blockchain.
This technology makes it possible to bring institutional trading activity on-chain while maintaining the privacy that traditional finance requires. Institutions can privately trade with other institutions globally, without having to touch public markets, enjoying the benefits of blockchain technology such as fast settlement and reduced counterparty risk, without exposing their trading intentions or volumes to the broader market.
Organizations can bring client accounts and assets on-chain while maintaining full compliance. This infrastructure protects on-chain asset trading and settlement strategies, ensuring that sophisticated financial operations remain private. A private world computer also supports private stablecoin issuance and redemption, allowing financial institutions to manage digital currency operations without revealing sensitive business information.
Users have granular control over their privacy settings, allowing them to fine-tune privacy levels for their on-chain identity according to their specific needs. The system enables selective disclosure of on-chain activity, meaning users can choose to reveal certain transactions or holdings to regulators, auditors, or business partners while keeping other information private, meeting compliance requirements.
The shift from transparent blockchains to privacy-preserving infrastructure is the foundation for bringing the next billion users on-chain. Whether you're a developer building the future of private DeFi, an institution exploring compliant on-chain solutions, or simply someone who believes privacy is a fundamental right, now is the time to get involved.
Follow Aztec on X to stay updated on the latest developments in private smart contracts and decentralized privacy technology. Ready to contribute to the network? Run a node and help power the private world computer.
The next Renaissance is here, and it’s being powered by the private world computer.
After eight years of solving impossible problems, the next renaissance is here.
We’re at a major inflection point, with both our tech and our builder community going through growth spurts. The purpose of this rebrand is simple: to draw attention to our full-stack privacy-native network and to elevate the rich community of builders who are creating a thriving ecosystem around it.
For eight years, we’ve been obsessed with solving impossible challenges. We invented new cryptography (Plonk), created an intuitive programming language (Noir), and built the first decentralized network on Ethereum where privacy is native rather than an afterthought.
It wasn't easy. But now, we're finally bringing that powerful network to life. Testnet is live with thousands of active users and projects that were technically impossible before Aztec.
Our community evolution mirrors our technical progress. What started as an intentionally small, highly engaged group of cracked developers is now welcoming waves of developers eager to build applications that mainstream users actually want and need.
A brand is more than aesthetics—it's a mental model that makes Aztec's spirit tangible.
Renaissance means "rebirth"—and that's exactly what happens when developers gain access to privacy-first infrastructure. We're witnessing the emergence of entirely new application categories, business models, and user experiences.
The faces of this renaissance are the builders we serve: the entrepreneurs building privacy-preserving DeFi, the activists building identity systems that protect user privacy, the enterprise architects tokenizing real-world assets, and the game developers creating experiences with hidden information.
This next renaissance isn't just about technology—it's about the ethos behind the build. These aren't just our values. They're the shared DNA of every builder pushing the boundaries of what's possible on Aztec.
Agency: It’s what everyone deserves, and very few truly have: the ability to choose and take action for ourselves. On the Aztec Network, agency is native
Genius: That rare cocktail of existential thirst, extraordinary brilliance, and mind-bending creation. It’s fire that fuels our great leaps forward.
Integrity: It’s the respect and compassion we show each other. Our commitment to attacking the hardest problems first, and the excellence we demand of any solution.
Obsession: That highly concentrated insanity, extreme doggedness, and insatiable devotion that makes us tick. We believe in a different future—and we can make it happen, together.
Just as our technology bridges different eras of cryptographic innovation, our new visual identity draws from multiple periods of human creativity and technological advancement.
Our new wordmark embodies the diversity of our community and the permissionless nature of our network. Each letter was custom-drawn to reflect different pivotal moments in human communication and technological progress.
Together, these letters tell the story of human innovation: each era building on the last, each breakthrough enabling the next renaissance. And now, we're building the infrastructure for the one that's coming.
We evolved our original icon to reflect this new chapter while honoring our foundation. The layered diamond structure tells the story:
The architecture echoes a central plaza—the Roman forum, the Greek agora, the English commons, the American town square—places where people gather, exchange ideas, build relationships, and shape culture. It's a fitting symbol for the infrastructure enabling the next leap in human coordination and creativity.
From the Mughal and Edo periods to the Flemish and Italian Renaissance, our brand imagery draws from different cultures and eras of extraordinary human flourishing—periods when science, commerce, culture and technology converged to create unprecedented leaps forward. These visuals reflect both the universal nature of the Renaissance and the global reach of our network.
But we're not just celebrating the past —we're creating the future: the infrastructure for humanity's next great creative and technological awakening, powered by privacy-native blockchain technology.
Join us to ask questions, learn more and dive into the lore.
Join Our Discord Town Hall. September 4th at 8 AM PT, then every Thursday at 7 AM PT. Come hear directly from our team, ask questions, and connect with other builders who are shaping the future of privacy-first applications.
Take your stance on privacy. Visit the privacy glyph generator to create your custom profile pic and build this new world with us.
Stay Connected. Visit the new website and to stay up-to-date on all things Noir and Aztec, make sure you’re following along on X.
The next renaissance is what you build on Aztec—and we can't wait to see what you'll create.
Special thanks to Palla, James Zaki, and Emmanuel Batse for the review.
Disclaimer: if you’re familiar with Account Abstraction and are curious about how it works on Aztec, go right to the section “The most abstract Account Abstraction”.
Account Abstraction context
What is AA and why did the Ethereum community give it this name?

Note: the second option is sometimes also referred to as “contract wallets” or “smart accounts”.
The story of Account Abstraction
AA on Ethereum
The discussions around AA on Ethereum started around 2017. There were a number of EIPs and ERCs proposing different versions of AA (e.g. EIP-86, suggesting abstraction of transaction origin and signature, EIP-1014, and EIP-2938) that were explored and discussed but ultimately rejected, so we won’t cover them in this piece.
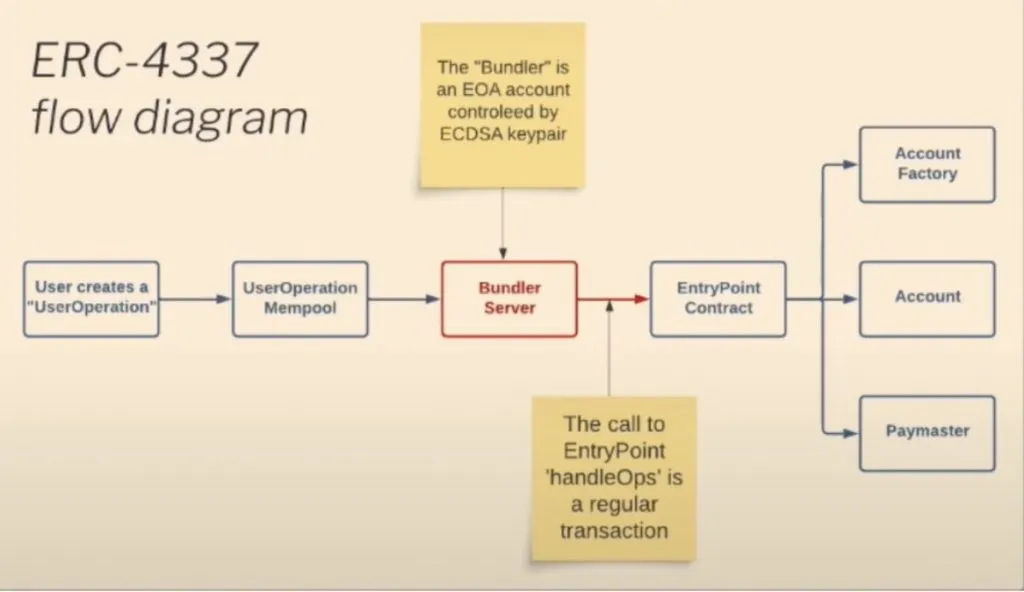
The first ERC affiliated with AA that made it to Ethereum mainnet was ERC-4337 (deployed on Mainnet in March 2023). It introduced AA without any modifications to the core protocol. It achieved this by replicating the functionality of the transactions mempool in a higher-level system. Instead of transactions, users send UserOperation objects to relayers, and these relayers package a set of these objects into a single standard transaction that is sent to Ethereum nodes.
Since then, the community has argued whether ERC-4337 is the Ethereum AA endgame or not. Right now, there is a dispute around EIP-3074 in the next Ethereum protocol upgrade. It suggests AUTH and AUTHCALL opcodes, which allow EOAs to delegate execution to smart contracts. However, one should note that the transaction validity still relies on EOAs’ ECDSA signature (i.e. ECDSA signature becomes enshrined).
This EIP is not new and some ecosystem players have discussed it being complementary to ERC-4337. The core question is what’s the more urgent problem for Ethereum to solve – censorship-resistance (against EIP-3074) or user experience (for EIP-3074)?
As Ethereum follows the rollup-centric roadmap, we expect most activity to happen on Ethereum L2s. As L2s technically don’t depend on Ethereum, they can implement AA on their own by introducing appropriate opcodes.
Some L2s have chosen a native AA “feature” as one of their core value propositions and implemented native AA (among those zkSync, StarkNet, and Aztec). In particular, this means that a transaction can be initiated directly by a smart contract (i.e. without any reliance on EOA).
As a comparison, in ERC-4337, AA is not native, as there is a step in the tx flow where an EOA account is engaged (as a Bundler).
As an alternative to enshrining AA in Ethereum, the Rollup Improvement Proposal (RIP) was proposed. RIP is a way to facilitate L2 standardization (not only around AA but around other L2 aspects as well). RIP-7560 is a native version of ERC-4337 for L2 chains currently under discussion. Check a series of RollCalls to learn more.
The most abstract Account Abstraction
While we talk about “arbitrary verification logic” describing the intuition behind AA, the logic is not really arbitrary. The verification logic (i.e. what can be checked as an authorization) is limited to make the verification time fast and bounded. That is the case for all chains where transaction validity is checked by the sequencer. Otherwise, it will cause UX downfall, whereas the main reason behind introducing AA is UX improvement.

On Aztec, there is no limitation on verification logic, as transaction validity check is executed client-side and a proof of validity is supplied to the sequencer. The sequencer only verifies the proof and this process is independent of the verification logic complexity.

This unlocks a whole universe of new use cases and optimization of existing ones. Whenever the dapp can benefit from moving expensive computations off-chain, Aztec AA will provide a unique chance for an optimization. That is to say, on traditional chains users pay for each executed opcode, hence more complex operations (e.g. alternative signature verification) are quite expensive. In the case of Aztec, it can be moved off-chain so that it becomes almost free. The user pays for the operations in terms of client-side prover time.
For example:

However, one should note that if the verification logic depends on the public state and requires a public function call (e.g. checking the balance), this check will be executed by the sequencer and imply some limitations on the allowed complexity of verification logic. For those who prefer watching over reading, here is a talk, “Account Abstraction for a Private Network”, by Santiago Palladino (Palla).ConclusionAA is not a new topic, however, AA on private networks unlocks new capabilities for arbitrary verification logic, allowing for more complex logic as well as significant cost optimizations. Check documentation to dive into the details of Aztec’s AA. And if you are up to join Aztec’s building pioneers – express your interest in this form. Sources
Aztec Labs is committed to enabling developers to build with ZK and unlock the full potential of this transformative technology. To that end, we built Noir, an open source Domain Specific Language for safe and seamless construction of privacy-preserving ZK proofs. We fund tooling, libraries, and applications that make Noir more accessible and enjoyable for developers.
Earlier this year, the Ethereum Foundation announced the first ZK Grants Round, a cofunded proactive grants round to encourage research and development for Zero-Knowledge proofs and standards for ZK L2s. Aztec Labs contributed US$150,000 to the US$900,000 prize pool alongside other projects such as Polygon, Scroll, Taiko, and zkSync. We sponsored this initiativeas a part of our commitment to support builders who are advancing ZK across dimensions including research, performance, tooling, and applications.
We were thrilled to see submissions to the ZK Grants Round from both new and existing Noir contributors. In this post, we want to highlight the ZK Grants Wave awardees for the Noir ecosystem to showcase what the community is working on and provide inspiration for how you could contribute.
Team: @eryxcoop, @manastech
Noir is back-end agnostic and its Arithmetic Circuit Intermediate Representation (ACIR) can be integrated with different proving backends. This project will enable Noir users to prove and verify their programs with Plonky2 technology, unlocking more possibilities to develop blockchain and ZK infrastructure with Noir. Meanwhile, it will also allow Plonky2 users to benefit from Noir’s developer-friendly abstractions, tooling, and growing sets of libraries, lowering the barrier of entry to the proving technology.
Team: @schaliasosvons, @theosotir
Noir abstracts away underlying cryptography so it’s accessible to a broader developer base. However, one risk of these abstractions is unintentionally leaking private variable information. This tool will apply static analysis, taint tracking, input generation, and SMT solving to detect privacy leaks in Noir program designs. Noir users can leverage this easy to use framework and debugging tool to identify, analyze and amend such leakages in their projects.
Team: @wz__ht
Performance benchmarking varies across different languages and proving systems. This project aims to produce benchmarking suites, articles, and a website that compares and informs developers about characteristics, performance, and tradeoffs between Noir-compatible and other proving backends in the ZK ecosystem.
Team: @wz__ht
Noir reduces barriers for developers to use ZK with its simple and familiar Rust-like syntax. But a solid developer experience is more than just language design. It also depends on a strong ecosystem of developer tooling. This project will offer treesitter grammars that unlock features like syntax highlighting and code formatting for the language in more development environments like Helix and Neovim – providing Noir developers with more flexibility and choice.
Team: Neoxham, Lakonema2000, @0x18a6
Noir tooling and libraries are created to support and enable application developers who solve problems using ZK. This team will leverage Noir to create an educational end-to-end example of verifiable Know Your Customer (KYC) with compliance checks, and provide onboarding guides to increase adoption of the application.
We are grateful to the Ethereum Foundation for coordinating the ZK Grants Round and to the teams who submitted proposals. We look forward to seeing how the Noir community leverages these tools and resources to build the next wave of ZK powered applications.
If you’d like to learn more about Noir, read our docs and follow @NoirLang for more contribution opportunities coming soon.
The proof generation for a privacy-preserving zk-rollup differs a lot from that of a general-purpose zk-rollup. The reason for this is that there is specific data in a given transaction (processed by private functions) that we want to stay completely private. In this article, we explore the client-side proof generation used for proving private functions’ correct execution and explain how it differs from proof generation in general-purpose rollups.
Contents
Disclaimer: If you’re closely familiar with how zk-rollups work, feel free to skip this section.
Before we dive into proofs on Aztec, specifically the privacy-first nature of Aztec’s zk-rollup, let’s recap how proofs work on general-purpose zk-rollups.
When a stateful blockchain executes transactions, it conducts a state transition. If the state of the network was originally A, then a set of transactions (a block) is executed on the network, the state of the network is now B.
Rollups are stateful blockchains as well. They use proofs to ensure that the state transition was executed correctly. The proof is generated and verified for every block. All proofs are posted on L1, and anyone can re-verify them to ensure that the state transition was done correctly.
For a general-purpose zk-rollup, proof generation is very straightforward, as all data is public. Both the sequencer and the prover see all the transaction data, public states are public, and the data necessary to reconstruct each state transition is posted on L1.
Aztec’s zk-rollups are a different story. As we mentioned in the previous article, in the Aztec network, there are two types of state: public and private.

Aztec smart contracts (written in Noir) are composed of two types of functions: private and public.
For both of these, we need proof of correct execution. However, as the anatomy of private and public functions is pretty different, their proof generation is pretty different too.
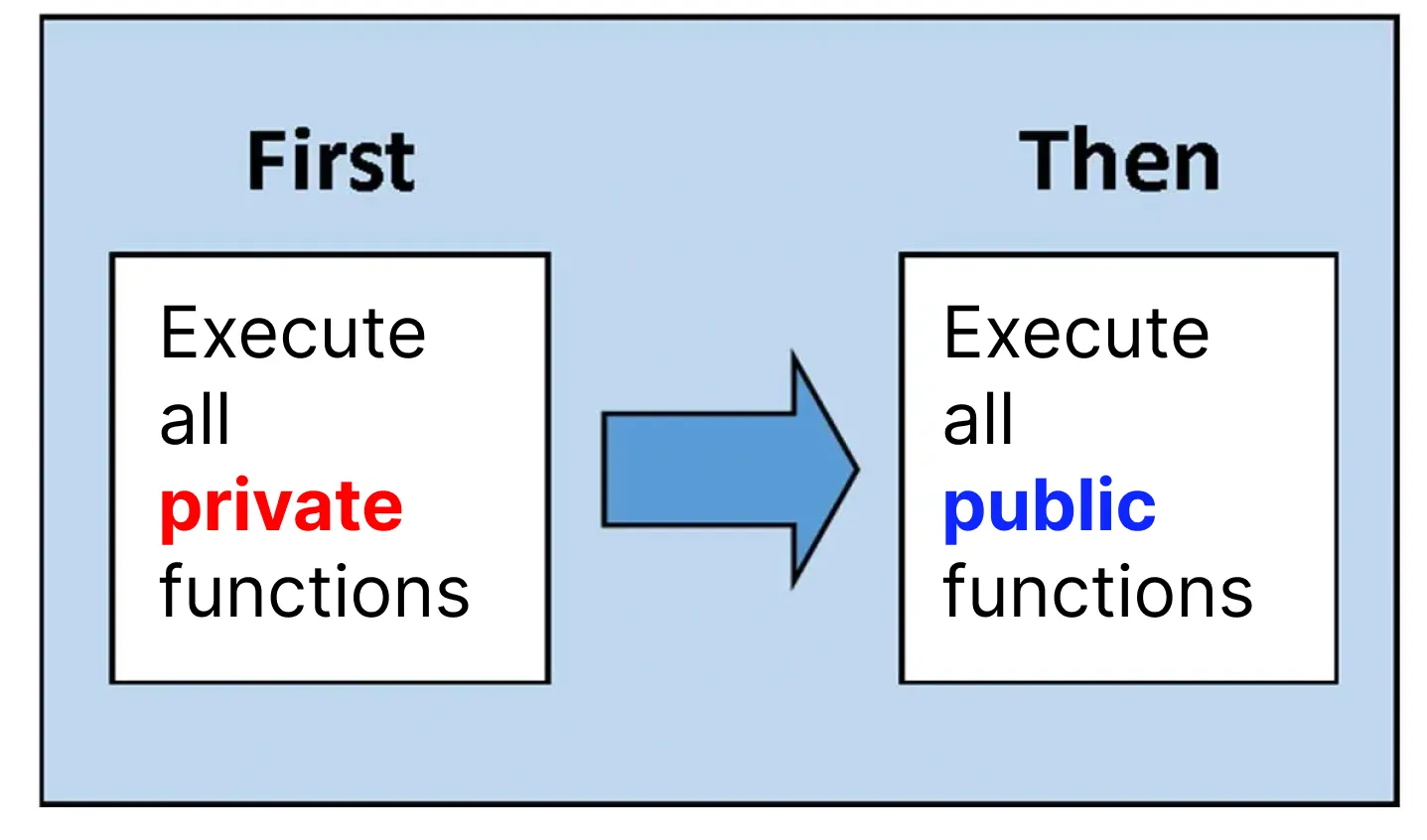
As a brief overview of how Aztec smart contracts are executed: first, all private functions are executed and then all public functions are executed.
However, diving into the anatomy of Aztec smart contracts is outside the scope of this piece. To learn more about it, check the previous article.
Here, we will focus on the correct proof generation execution of private functions and why it is a crucial element of a privacy-first zk-rollup.
The concepts of private state and private functions in blockchain might seem a little unusual. The following map describes the path of this article, where we will shed some light on the difference between how proofs work for private and public states respectively.
Let’s start by looking at public function execution, as it is more similar to other general-purpose zk-rollups.
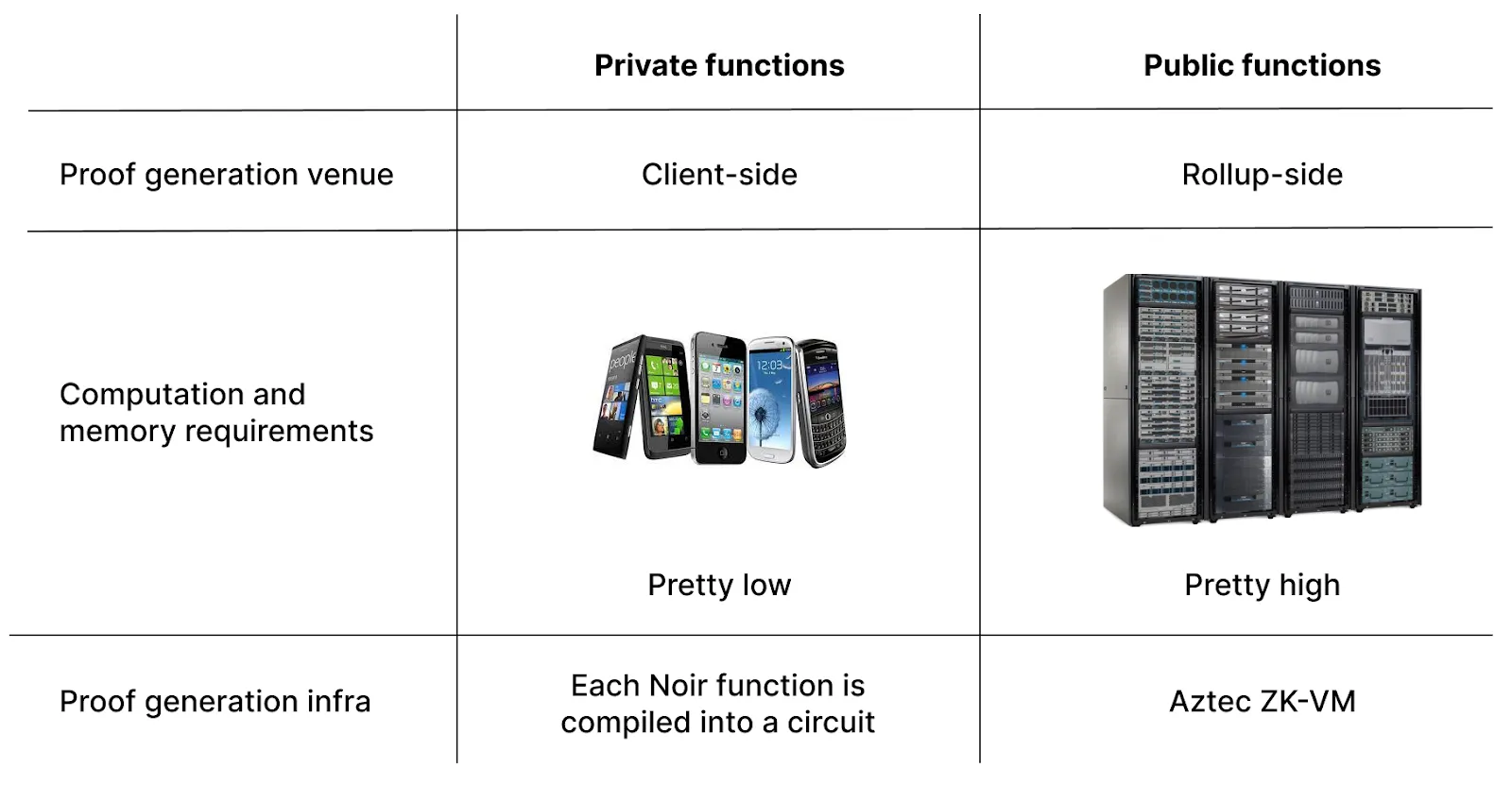
Public state is the global state available to everyone. The sequencer executes public functions, while the prover generates the correct execution proof. In particular, the last step means that the function (written in Noir) is compiled in a specific type of program representation, which is then evaluated by a virtual machine (VM) circuit. Evaluated means that it will execute the set of instructions one by one, resulting in either a proof of correct execution or failure. The rollup-side prover can handle heavy computation as it is run on powerful hardware (i.e. not a smartphone or a computer browser as in the client-side case).
Private state on the other hand is owned by users. When generating proof of a private transaction's correct execution, we want all data to stay private. It means we can’t have a third-party prover (as in the case of public state) because data would be subsequently exposed to the prover and thus no longer be private.
In the case of a private transaction, the transaction owner (the only one who is aware of the transaction data) should generate the proof on their own. That is, the proof of a private transaction's correct execution has to be generated client-side.
That means that every Aztec network user should be able to generate a proof on their smartphone or laptop browser. Furthermore, as an Aztec smart contract might be composed of a number of private functions, every Aztec network user should be able to generate a number of proofs (one proof for each private function).
On the rollup side, block proofs are generated using ZK-VM (ZK virtual machine). On the private side, there is no VM.
Instead, each private function is compiled into a static circuit on its own.
When we say “a circuit”, we’re referring to a table with some precomputed values filled in. This table describes the sequence of instructions (like MUL and ADD) to be executed during a particular run of the code.
There are a bunch of predefined relations between the rows and columns of the table, for example, copy constraints that state that the values of a number of wires are expected to be the same.
Let’s take a look at a quick example:

In the diagram above, we have two gates, Gate 1 (+) and Gate 2 (x). As we can see, z is both the output of Gate 1 (denoted as w3, wire 3) and the left input to Gate 2 (denoted as w4, wire 4). So, we need to ensure that the value of the output of Gate 1 is the same as the value of the left input of Gate 2. That is, that w3 = w4. That’s exactly what we call “checking copy constraints”.
When we say that the verifier verifies the circuit, we mean it checks that these predefined relations hold for all rows and columns.
Disclaimer: the following example reflects the general logic in a simplified way. The real functions are much more complex.
Assume we have a function a2+b2=c2. The goal is to prove that equality holds for specific inputs and outputs. Assume a = 3, b = 4, c = 5.
As a piece of code, we can represent the function as the following:

When the function is executed, the result of each step is written down in a table. When this table is filled with the results of the specific function execution on specific values, it’s called an execution trace.

This is just a fragment of the table, with values and opcode names. However, to instruct the computer about which operation should be executed in which specific row, the opcode name is not enough; we need selectors.
Selectors are gates that refer to toggling operations (like an on/off switch). In our example, we will use a simplified Plonk equation with two selectors: qADD for the addition gate and qMUL for the multiplication gate. The simplified Plonk equation is: qMUL(a*b)+qADD(a+b)-c=0.
Turning them on and off, that is, assigning values 1 and 0, the equation will transform into different operations. For example, to perform the addition of a and b, we put qADD= 1, qMUL=0, so the equation is a+b-c =0.
So, for each performed operation, we also store in the table its selectors:
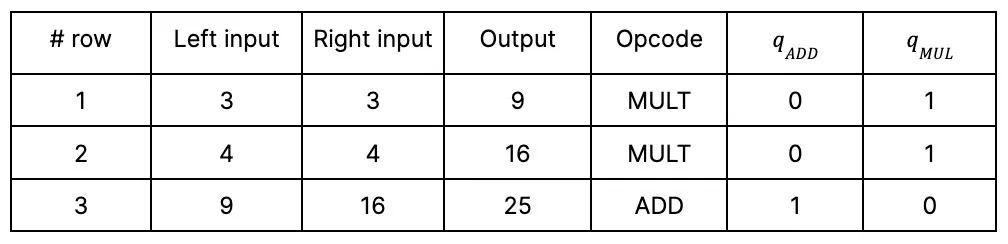
In the case of private functions, as each function is compiled into a static circuit, all the required selectors are put into the table in advance. In particular, when the smart contract function is compiled, it outputs a verification key containing a set of selectors.
In the case of a smart contract, the circuit is orders of magnitude larger as it contains more columns with selectors for public function execution. Furthermore, there are more relation checks to be done. For example, one needs to check that the smart contract bytecode really does what it is expected to do (that is, that the turned selectors are turned according to the provided bytecode commitment).
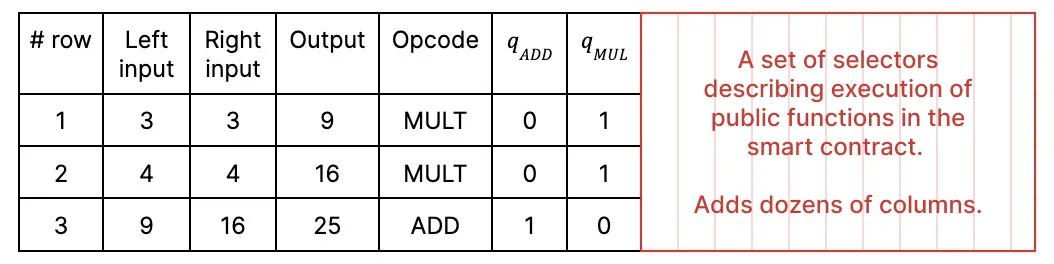
As a mental model, you can think about a smart contract circuit as a table where 50 out of 70 columns are reserved for the selectors' lookup table. Storing the entire table requires a lot of memory.
Now you see the difference between circuit size for client-side and rollup-side proof generation: on the client-side, circuits are much smaller with lower memory and compute requirements. This is one of the key reasons why the proofs of private functions' correct execution can be generated on users’ devices.
Client-side proof generation is a pretty novel approach for the blockchain domain. However, for privacy-preserving solutions, it is an absolute must-have. Aztec Labs has spent years developing the protocol and cryptography architecture that make client-side proof generation performance feasible for the production stage.
You can help build it further.
The following is written by Zac Williamson, with inspiration and advice from Arnaud Schenk.
My fellow companions, my decentralized brothers and sisters. I wish to tell you a story, about complicated people and their struggles to resolve the wreckage of their contradictions. It is a story of humanity.
We are at a unique point in history and stand at the threshold of two worlds. One world is a propagation of our present, a status quo antebellum with all of its associated joys and sorrows.
There is another door, one hidden from view except for those with the sight to see it. You and I are here because we see a unique vision of the future, one of high technology and high ideals, that advance human beings from their status as a commodity resource in a globalized world, to free actors imbued with autonomy and purpose, who bow to no one.
I want to articulate this vision and examine the forces that drive us. Despite our successes and dedication it is clear that our current achievements fall short of our aspirations. We must reconcile this.
Bitcoin is not yet a credible threat to traditional currencies. Paying for goods and services with cryptocurrency is a niche luxury for the technologically well-connected. Decentralized autonomous organizations (DAOs) are yet to govern anything that is not a cryptocurrency project. A notable exception was ConstitutionDAO, which immediately failed in its goals due to the intrinsic limitations of trustless blockchain networks.
There are missing pieces in the technological armaments we have fashioned. I want to show you the missing pieces. I want to go back to the roots: what are the systems and frameworks we want to disrupt? Which properties do blockchain networks need for us to forge a conspiracy against the present, and fight for our vision of the future?
Reaching back into prehistory, humanity has been waging a war against itself – a war that pits the freedom and autonomy of individuals against the safety and control of institutions.
We want to be free. We want to be safe. This is the eternal contradiction.
To acquire safety we bind ourselves to institutions. Within these institutions, control factions form. They metastasize and act to entrench their power and influence by monopolizing human agency. This triggers inevitable conflict and revolt, which acts to reset the equilibrium.
How best we can resolve the contradiction between freedom and safety is a function of social organization, the quality of which is gated behind technological innovation.
Blockchain is one such technology. To identify what we need, we must identify the weaknesses of the institutions we seek to undermine, and tailor our strengths against them.
Control factions have a fatal weakness: they reject competence.
Competent people threaten individuals within entrenched power structures. A competent subordinate is a threat to your power and privileges. This is the so-called “dictator trap”, but the mechanics at play extend to all power structures, from the boards of mega-corporations to the local residents association. But it’s not a dictator trap, it is an institution trap.
Power craves legibility and predictability and will act on these desires by exerting control – limiting agency and freedom of action.
We want to undermine institutional control, and redistribute control down to smaller units of organization.
Blockchain technology enables such radical new forms of social organization that fall outside the frameworks of traditional institutions.
We possess a keystone technology that enables mass peer-to-peer coordination, initially of cryptocurrency assets but this can be generalized to anything with perceived value that can be given a digital fingerprint.
Blockchain networks have radically different incentive mechanisms to traditional modes of social organization.
Because blockchains are coordination engines. They enable individuals to coordinate on how to deploy their collective resources. This type of mass-coordination of personal resources is unique and will subtly act to profoundly re-distribute the existing power structures of the present.
Why? Blockchains weaken the fundamental value propositions of vertically integrated companies that extract a profit from information asymmetries. Individuals whose skills serve large institutions can more easily decide for themselves how best to apply their skills, without the need for the institution’s support frameworks. As a coordination engine, blockchain networks can efficiently combine the skills and capital required to execute grand ideas, as well as provide a digital market for resulting products.
A global marketplace of programmable money is one with profound information transparency. The ability of independent groups to analyze the market enables great efficiency and reduces information asymmetries. Though, does not delete them entirely.
In short, blockchain networks are pro-competency. They allow individuals to decide for themselves how their skills can best be utilized and deployed, instead of having that decided for them by a control faction. Competent people add value to the network and in doing so, provide another composable brick that others can use in their constructions. The raw incentives create a positive-sum game.
What are the missing pieces?
The great difficulty in realizing our vision is the limited ability of current blockchains to reach into the real world.
We are not our online avatars. We exist in a physical space and we have physical needs that must be satisfied. We are bound to networks of obligation and responsibility that societies depend upon to maintain social order. We cannot live in an NFT.
The real world matters. Without a way of linking real-world identities to blockchains, the grand cypherpunk vision for blockchain can never be fully realized – only a neutered form of primitive electronic sovereignty.
The new information networks we are building lack a key ingredient: composable privacy.
By using novel cryptography, we can turn blockchains into encrypted ledgers where transactions hide their execution from observers. Identities can be encrypted, but still used to prove statements about the user, and without involving an additional institutional third party. e.g. “I have a U.S. passport”, “I have a digital driving license”, “I have a Twitter account with over 1,000 followers”, “I signed in with a Google account”.
The effect of this is to build trust infrastructure that allows human beings to iteratively build trust between themselves and to do so rapidly and at scale.
Programmable private blockchains stand to usher in a revolution in how distributed systems can be used. Without strong identity guarantees, the only workable governance mechanisms for distributed on-chain organizations are autocracy and plutocracy.
However, if past actions can be uniquely tied to a cryptocurrency account, it is possible to identify key stakeholders and to give them an accelerated role in governance. That enables a much more democratic architecture of governance systems.
Privacy technology is required to turn blockchains into the coordination engines they were always destined to be.
The future we are building does not outright destroy existing systems of control – it breaks them apart and replicates these systems on a smaller scale. Lower barriers to entry lead to greater competition and market fragmentation and act to limit the ability of distributed organizations to consolidate power.
Because coordination engines are pro-competency.
There is a phrase I think we will hear much of over the coming years: privacy for the user, transparency for the protocol.
The capabilities of private programmable blockchains and the outcomes they enable are not commonly understood. A private blockchain is not one where all information and data are intrinsically hidden. They are hybrid systems where public and private data coexist. Application designers and users can choose which data is hidden.
Efficient markets require data transparency. Data relating to identity requires data confidentiality. The solution is applications where information that relates to assets is public, and information relating to users (e.g. who owns said assets) is private.
To create a privacy-preserving ecosystem it must be possible for confidential, transparent, and hybrid applications to directly interact with one another. Privacy is not an aftermarket add-on to be bolted onto a few select applications. Full composability is essential to develop a rich ecosystem.
Composability enables trust-building networks by allowing individuals to put core aspects of themselves on-chain, disclosing it only selectively and enabling distributed protocols to use these capabilities in a composable permissionless manner, without leaking information. Who are you? What have you done? What do you want to do? With privacy, we can disclose this information to smart contracts and hide it from people. These will form core primitives of our new information networks.
I have spent the last 6 years building exactly this, through building Aztec. Crafting the missing ingredient, privacy, via cutting-edge cryptography, zero-knowledge proofs, and raw engineering.
Networks have values that are independent of their creators. Networks live or die on the quality of their network effects. This incentive gives network participants a shared motivation to expand the network. The more nodes that exist, the greater the value individual nodes can extract from the network. The manner in which the network changes itself to act on these motivations defines its intrinsic values.
What are the intrinsic values of permissionless programmable privacy networks like Aztec? We can derive these from the fundamental value proposition – to expose a rich ecosystem of composable, confidential applications, and to do this as a permissionless, decentralized network. This enables individuals and small groups to compete in industries dominated by large players leveraging large information asymmetries.
Such networks are, at their very core, pro-competency. If you have something useful to add to the network, you can. If you want to use existing network components in your product, go right ahead. No need to ask for permission from the network.
From this starting point we can anticipate the cycles of action and reaction that will drive networks like Aztec to adopt the following values over their lives:
Blockchain networks grow by harnessing the industry and enterprise of as many human souls as they can get their hands on.
Without mechanisms of coercion to fall back on, the network must ensure a positive-sum game for network participants who add value. These also happen to be values that I believe I strongly hold. This is not a coincidence. I started in web3 seven years ago building a marketplace for corporate debt on Ethereum and by degrees ended up building a distributed programmable privacy network on Ethereum. This was not due to some grand design but, I think, the cumulative effects of seven years of following my impulses. To find a place of belonging.
This feeling is something you may share – that the frameworks and systems produced by our societies offer none of us a true sense of belonging and purpose. But here, amongst our companions, we have found belonging through building a shared vision of a radical new world.
There is a long road to walk to realize the ambitions of the new information networks. The technology is barely capable and challenging to build. The architecture is novel and challenging to design. Convincing people to build on radical foundations to bootstrap a market is challenging. Building competitive infrastructure and tooling is challenging.
The challenge is irrelevant. We cannot become a generation scorned by our descendants for squandering the opportunity of a lifetime.
We will build and deploy the new information networks and by degrees will learn how to use them to chip away at the inequities of the status quo, and the social order that upholds it.
Equipped with such armaments and driven by our ideals, we will pull our ideas into reality. Together, we will forge our digital Eden.